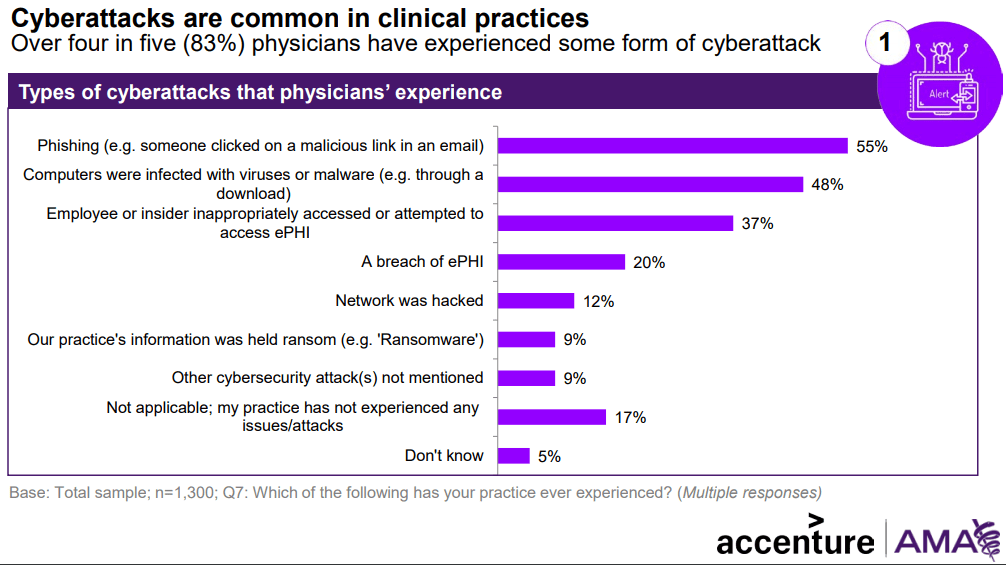
For healthcare providers, securing electronic protected health information (ePHI) has become more complex with the widespread adoption of telemedicine .As ePHI is now transmitted in real time over digital platforms, the landscape of data protection and regulatory compliance has changed significantly. While telemedicine offers faster patient communication and improved access to care, it also introduces new risks, particularly around data security.
A single breach can result in serious consequences, especially if providers fail to follow HIPAA guidelines on telemedicine.
Fortunately, many of these risks can be reduced by adhering to the official HIPAA framework for telehealth. But what exactly do the HIPAA guidelines on telemedicine require? Let’s explore the key considerations. (more…)