Todays security blog puts forth a litany of eye-glazing Cybersecurity terms like Macro-Laden, OpenDNS, Social Engineering, and its ilk. But stick around till the end, as well detail how hackers continue to exploit both system and human vulnerabilities, and point out a few security layers that exist to foil their attempts.
Category: Cyber Attacks
Stay updated on cyber attacks worldwide. Explore expert insights, threat trends, and prevention strategies to protect your business from evolving cybersecurity risks.
-

Don’t Leave Hackers A Path To Follow
Don’t leave hackers a path to follow! Encrypting credit card # in POS reader hardware enables secure processing from the start & doesn’t allow malware installation. #pcicompliance
-

Are your web apps insecure low hanging fruit?
Are your web apps insecure low hanging fruit? Fortify your online storefront as securely as you would your brick-n-mortar business. Migration to EMV shifts hacker focus to online fraud. PEN test your web apps and implement a business-grade Web Application Firewall!
-

Hackers Now Shifting from POS to Card-Not-Present Fraud
Few things are more sought-after by hackers than private credit card and payment data, Stealing credit and debit card numbers for fraudulent use is as popular as ever with cybercriminals. And recent data suggests they’re increasingly turning to card-not-present fraud.
-

Are banks overconfident in their ability to protect against cyber threats?
Are banks overconfident in their ability to protect against cyber threats? According to Accenture’s 2016 Global Survey on High Performance Security, 80% of banking respondents are confident facing cyber threats, yet 1 in 3 breach attempts succeed. Only 13% of banking respondents cited investment in Cybersecurity training.
Don’t rest on cyber-laurels, seek continuous Cybersecurity training!
-
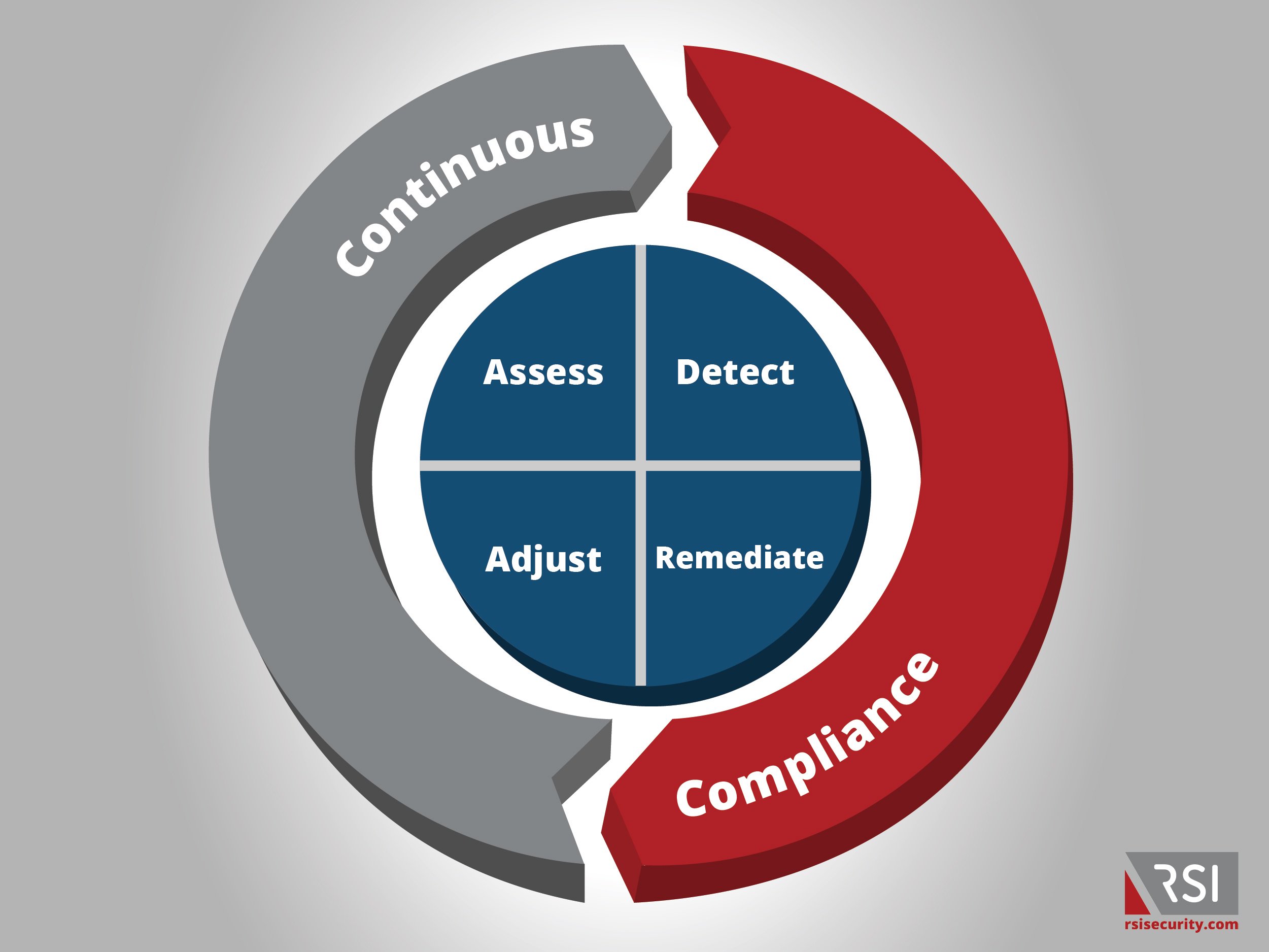
Single “Point-in-Time” Compliance Doesn’t Equal Secure
Given the recent Kmart security breach of credit card numbers being compromised we can see that persistent vigilance is essential given evolving malware threats. Single “Point-in-Time”compliance doesn’t equal “Secure”.
As you can see in the chart below it is essential to continuously asses the degree to which your business is being compliant. There should be a constant cycle of assessing, detecting, adjusting, and remediating to ensure that your business stays secure from malicious hackers.
-

Breaches are Increasing but Investments Stay Stagnant
Cybersecurity threats are ever increasing yet the investment in increasing security measures is staying the same. 87% of Finance execs expect rise in breaches but only 49% will increase spend!
-

How the Hospitality Industry is Getting Hacked
Hotels & Restaurants Hospitality segment is plagued by Point-of-Sale incidents, opportunistic hackers are stealing financial PII. Businesses are lacking an IT dept but still accepting credit cards, making Hospitality SMBs (Small to Medium Businesses) a prime mark. Installation of scraper takes seconds but detecting, containing the breach, and mitigating impact could take months.
-
Infographic: How prepared is your business to face cyber threats?
Continued recognition, vigilance, and preparedness against evolving Cyberthreats are key to building up a robust Threat Management posture.
-
Default is the Enemy & Backups are your Friend
There was a time not so long ago that any time one needed a Wi-Fi signal, we had our pick of networks to join. By our count, approximately 5% of available SOHO (Small Office, Home Office) networks were entirely unsecured / lacked a password! Then, seemingly almost overnight, it was nearly impossible to find an unsecured, open WiFi network.