Over the past decade, the healthcare industry has undergone a major shift from paper records to electronic health records (EHRs). In 2008, fewer than half of healthcare organizations used EHR systems. Today, thanks to the Health Information Technology for Economic and Clinical Health Act of 2009 (HITECH), digital records are now the standard across hospitals, clinics, and physician offices. While EHR adoption has modernized healthcare operations and improved patient care, it has also introduced new cybersecurity Security Breaches . As healthcare organizations store increasing amounts of sensitive patient information online, the risk of healthcare security breaches has grown significantly.
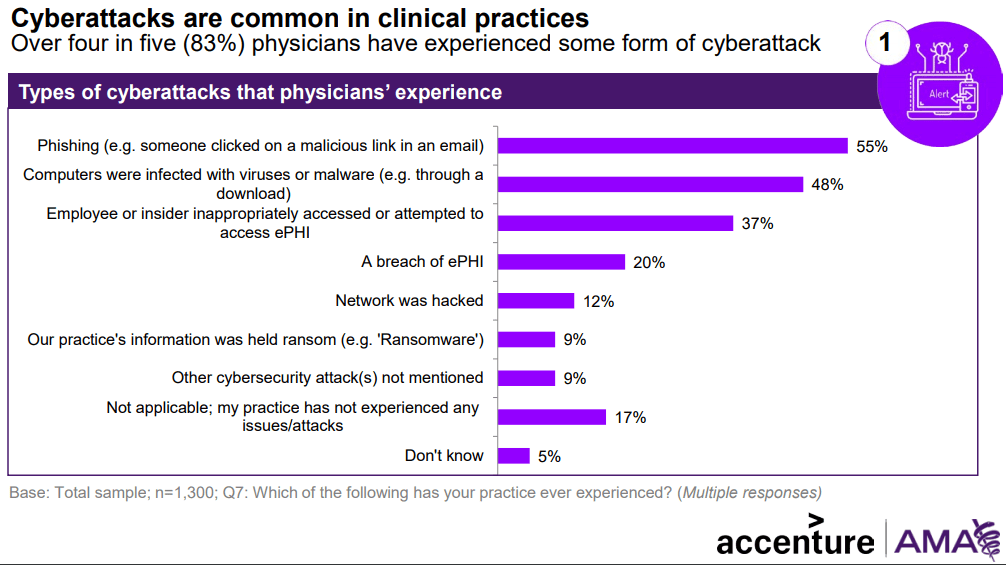
Since the HITECH Act strengthened penalties for noncompliance, the number of reported healthcare breaches has risen steadily. In 2010 alone, the number of reported incidents exceeded the total from the previous six years combined. Although the spike was initially attributed to rapid EHR adoption, it is now clear that several factors contribute to the growing risk of healthcare security breaches. With the widespread use of digital tools—including smartphones, cloud storage, connected medical devices, and complex network systems—cybersecurity threats in healthcare have become more sophisticated. Understanding the causes of healthcare security breaches is essential for protecting electronic protected health information (ePHI) and strengthening healthcare cybersecurity defenses. (more…)