In today’s competitive business environment where small and large businesses alike must compete with megaliths like Walmart and Amazon, creating a strong brand is key to maintaining a strong customer base. Of course, there are many aspects that you could implement to build a positive brand, but security for any company that handles or stores customer data or transactions is a key element of a positive brand.
If you want to be taken seriously as a business owner, you must ensure that security is a top priority as one customer data security study conducted by digital security expert Gemalto found. Out of the 10,000 customers they surveyed, only 27 percent of consumers felt that businesses take customer data security very seriously. Additionally, 70 percent of consumers said that they would altogether stop doing business with a company if it experienced a data breach.
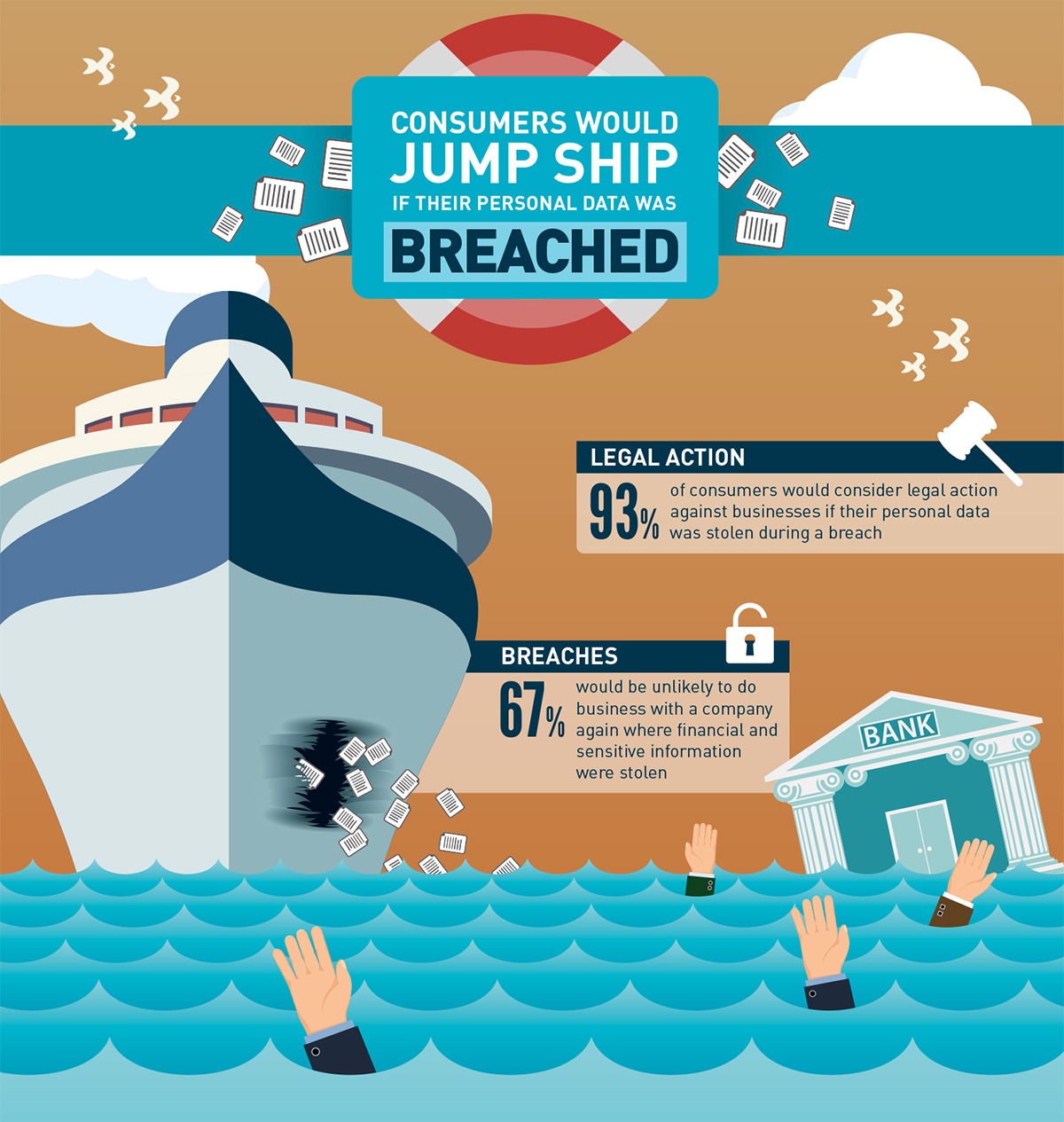
Image source: https://www.gemalto.com
Preventing the Sinking Ship
The truth is when customers interact with your business, rarely do they think of security. In fact, security is usually the last thing on someone’s mind until, well, it becomes the first thing on their mind. When Mr. Phillip Franklin, vice president of the International Mercantile Marine, which controls the White Star Line (under which the Titanic was operated) issued the statement, “we are perfectly satisfied that the Titanic is unsinkable,” the passengers certainly believed him. Far more interested in the amenities aboard the ship — including a gymnasium, Turkish bath, a squash court, and lavish decorations — the passengers paid little attention to the fact there were far too few lifeboats aboard the ship and an untrained crew.
However, passengers would pay attention to this detail after the ship collided with a large iceberg and quickly took on water. The supposed “unsinkable” ship sunk. Stricter regulations were quickly put in place after the disaster, but no one wants to be the company that is held up as an example of what not to do.
Think of security certifications as both necessary tools to help prevent a disaster and (should one occur) mitigate any major damage to your business/customer data. Even if your company provides all the fanciest amenities to your clients, having a security certificate shows your customers that those amenities are fully protected.
Assess compliance in your industry
Meeting Security Certificate Requirements
One of the major issues that resulted in so many deaths on the Titanic was the lack of lifeboats on board. David Hutchings author of RMS Titanic 1909-12 writes, “[the] Titanic only had enough lifeboats to carry about half of those on board; if the ship had carried her full complement of about 3,339 passengers and crew, only about a third could have been accommodated in the lifeboats.”
If your company is not meeting basic security requirements, how can your customers trust that their personal information or transactions will be secure? Just like the lack of lifeboats on board, insufficient online security for your business can lead to catastrophic ends.
Depending on your business and services you provide security certifications will vary. From financial to cloud security to patient health information privacy, each certification is a useful marker of a trusted brand.
1. Payments Platforms and Providers
Two major financial certifications that you should be aware of if you provide financial services to your clients are PCI DSS and FINRA.
PCI DSS Compliance
The Payment Card Industry Data Security Standard (PCI DSS) is a security standard for organizations that use major credit cards including Visa, MasterCard, American Express, Discover, and JCB for transactions—both on and offline.
Approved PCI DSS compliance scanning vendor, RSI Security points out that, “whether you are a large or small business, if you are a merchant who accepts credit card payments or are a service provider to merchants, your organization is responsible and must protect payment cardholder data through PCI security standards and PCI services.”

Image source: https://stripe.com
Take the online payment company Stripe as a good example of a brand that offers both a variety of amenities to its customers but also, “has been audited by a PCI-certified auditor and is certified to PCI Service Provider Level 1.” Security at Stripe is taken seriously, as PCI Service Provider Level 1 certification is the most stringent level of certification available in the payment industry. Read more into compliance offerings for the financial sector to better understand why working with a company like RSI Security offering PCI DSS compliance is so critical.
In the example of Stripe, they were able to build helpful applications atop their payment platform because they focused on achieving compliance standards.
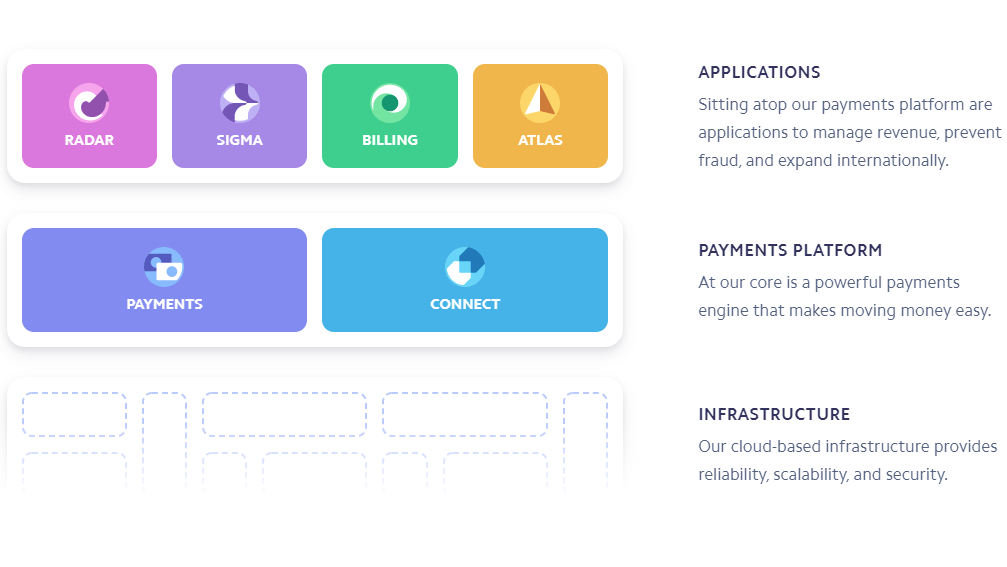 Image source: https://stripe.com
Image source: https://stripe.com
FINRA Compliance
The Financial Industry Regulatory Authority (FINRA) helps protect investors by guaranteeing that the broker-dealer relationship is fair and honest. This non-profit organization approved by Congress and with an oversight committee from the Securities Exchange Commission focuses on creating a positive investment environment for both firms and private investors.
There are a number of other financial certifications you can obtain to brand your company as a trusted source. Improving financial institution cybersecurity is critical as the finance and insurance fields were the most targeted industries of 2018 cyber-attacks according to IBM X-Force Threat Intelligence Index of 2019.
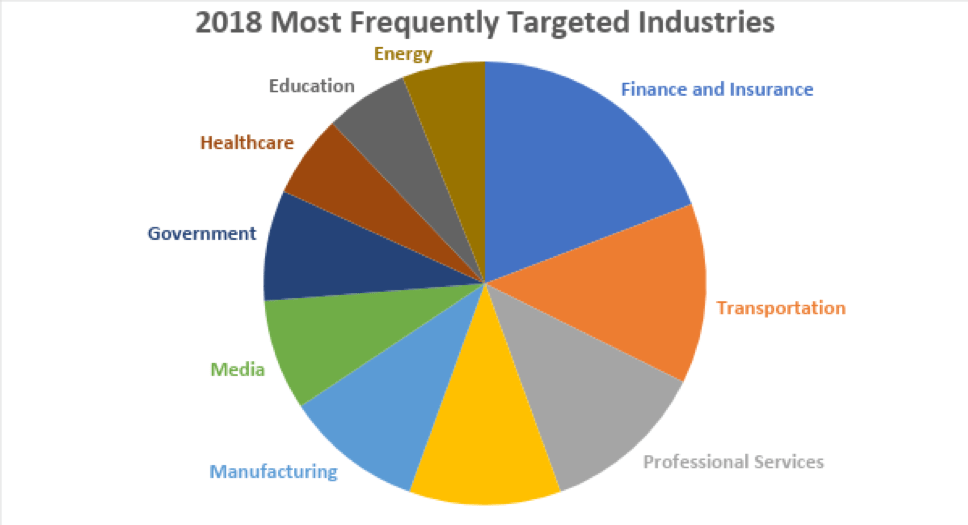
Image source: https://blog.rsisecurity.com/how-to-improve-cybersecurity-in-financial-institutions
2. Healthcare Organizations
Healthcare organizations must also consider their brand as they handle patients’ health. Quality of care, ease of billing, and responsive customer service are important aspects of a strong healthcare brand. Additionally, protecting patients’ private information is also crucial to maintaining trust. Healthcare certifications such as HIPAA or HITRUST indicate a company takes care to protect its patients’ data.
HIPAA Certification
If you are a business provides treatment, operates in healthcare, provides support in payment or treatment, are a healthcare business associate or subcontractor, operates in healthcare, or exists as a covered entity (this includes: health plans, health care clearinghouses, health care providers) then you must be HIPAA compliant at all times.
Any of these businesses must comply with HIPAA compliance requirements; keeping HIPAA compliance up-to-date is an important element of meeting the requirements. If a business does not meet these standards, they may face criminal charges or significant fines; this is true even if the business willfully breaks the law or out of negligence. Understanding HIPAA rights and obligations will guarantee that you provide the best care for your clients.
HITRUST Certification
The HITRUST approach is best understood as a comprehensive framework that meets compliance requirements for multiple regulatory certifications. In this way, HITRUST certification can provide more in-depth protection than just meeting HIPAA requirements. The difference between HITRUST and HIPAA at its core is that HITRUST is a more rigorous and comprehensive certification process than just HIPAA alone.
 Partnering in the past with the American Medical Association (AMA), the HITRUST Alliance has long focused on improving the healthcare provider’s relationships with its clients. “As cyber threats continue to increase, the AMA believes it is important to arm small practices with the tools they need to keep their practices – and their patients’ information – secure,” said AMA President David O. Barbe, M.D. “We look forward to working with HITRUST to help small practices manage the cybersecurity challenges they may be facing.”
Partnering in the past with the American Medical Association (AMA), the HITRUST Alliance has long focused on improving the healthcare provider’s relationships with its clients. “As cyber threats continue to increase, the AMA believes it is important to arm small practices with the tools they need to keep their practices – and their patients’ information – secure,” said AMA President David O. Barbe, M.D. “We look forward to working with HITRUST to help small practices manage the cybersecurity challenges they may be facing.”
3. Higher Education Institutions
When people pick out a university to attend they usually just look at the majors and minors, facilities, sports programs, cost, and similar factors. Nevertheless, with the high amount of private data a higher education institution handles, it’s important that they follow strict standards for safeguarding that data. Two certificates including the GDPR for universities with international students and the CCPA for California universities indicate a school’s dedication to protecting its students’ information.
GDPR Certification
The General Data Protection Regulation (GDPR) is a legal framework that sets guidelines for the collection and processing of personal information of the European Union (EU) data subjects. This regulation serves to protect the freedoms and rights of EU citizens by protecting private information. Should an institution fail to comply, they are subject to fines.
CCPA Certification
Data is ubiquitous. From small purchases we make at fast-food restaurants – to the websites we visit and texts we send – a treasure trove of data is waiting to be mined. In 2018, with a unanimous vote, California created an act that would help protect Californian’s private information.
The California Consumer Privacy Act restores the power to the consumer to handle their data as they choose allowing them to control the use and sale of their data. Some of the key provisions of this act include:
- Consumers’ right to know and access personal data
- Right to deletion
- Right to Opt Out / Opt In
- Right to equal service
- Privacy Policy Requirements
- Disclosure requirements
- GLBA/HIPAA/Research/Legal Exceptions
As this is a newer act only incorporated last year, you may not be as familiar with the requirements. Privacy policy requirements for CCPA include six primary requirements for certification. In addition to the helpful guide linked, RSI Security can help you determine if your Californian company is complying with the requirements of the Privacy Act.
4. Accountants and Tax Preparers
If you are an accountant or a tax preparer who files client taxes online, you should be aware of the security standards required to maintain client data. The IRS introduced the E-file Privacy and Business Standards to serve taxpayers by protecting their personal information. Some of the standards set by the IRS for accountants and tax preparers include:
- Setting minimum encryption standards for electronic transmission of taxpayer data
- Conducting periodic external vulnerability scans of the taxpayer data environment
- Protecting against “bulk filing” of fraudulent income tax returns
- Timely isolation and investigation of potentially compromised taxpayer information
- Reporting of Security Incidents to the IRS
TurboTax® is a good example of a company that focuses on protecting its customers’ data by obtaining security certificates. As an authorized E-file provider, a customer knows that they follow the stringent standards set by the IRS.
Image Source: https://turbotax.intuit.com/best-tax-software/secure-online-tax-prep/
5. Cryptocurrency Exchanges
Whether or not you fully understand cryptocurrencies like Bitcoin or Ethereum, they have cemented themselves as a viable currency. Just like any currency, trusted authentication standards ensure purchasing power. As an effort to regulate this new market industry experts established standards that help ensure a balance of openness & privacy, security & usability, and trust & decentralization.
The Cryptocurrency Certification Consortium (C4) is one group working on creating a fair system in which buyers and sellers can exchange cryptocurrency with confidence. CryptoCurrency Security Standard (CCSS) is a set of requirements for all information systems that make use of cryptocurrencies, including exchanges, web applications, and cryptocurrency storage solutions.
There are three levels of increasing security to manage any cryptocurrency exchange. Those levels detailed by the C4 group in their open standard repository are as follows.
Level 1
“An information system that has achieved Level I security has proven by way of audit that they protect their information assets with strong levels of security. Most risks to the system’s information assets have been addressed by controls that meet industry guidelines. While this is the lowest level within CCSS, it still represents strong security.”
Level 2
“An information system that has achieved Level II security has proven by way of audit that they exceed strong levels of security with additional enhanced controls. In addition to covering most risks to the information system’s assets, the use of decentralized security technologies such as multiple signatures has been employed which exceed industry guidelines and provide redundancy if any one key or person becomes unavailable or compromised.”
Level 3
“An information system that has achieved Level III security has proven by way of audit that they exceed enhanced levels of security with formalized policies and procedures that are enforced at every step within their business processes. Multiple actors are required for all critical actions, advanced authentication mechanisms ensure the authenticity of all data, and assets are distributed geographically and organizationally in such a way to be resilient against compromise of any person or organization.”
CCSS Audit
When performing a CCSS audit, an external auditor will test a variety of security aspects for their level of protection. In the example below, Acme Exchange indicated meeting standards for level three with specific security aspects, however, across the board it only met the necessary standards for level one certification.
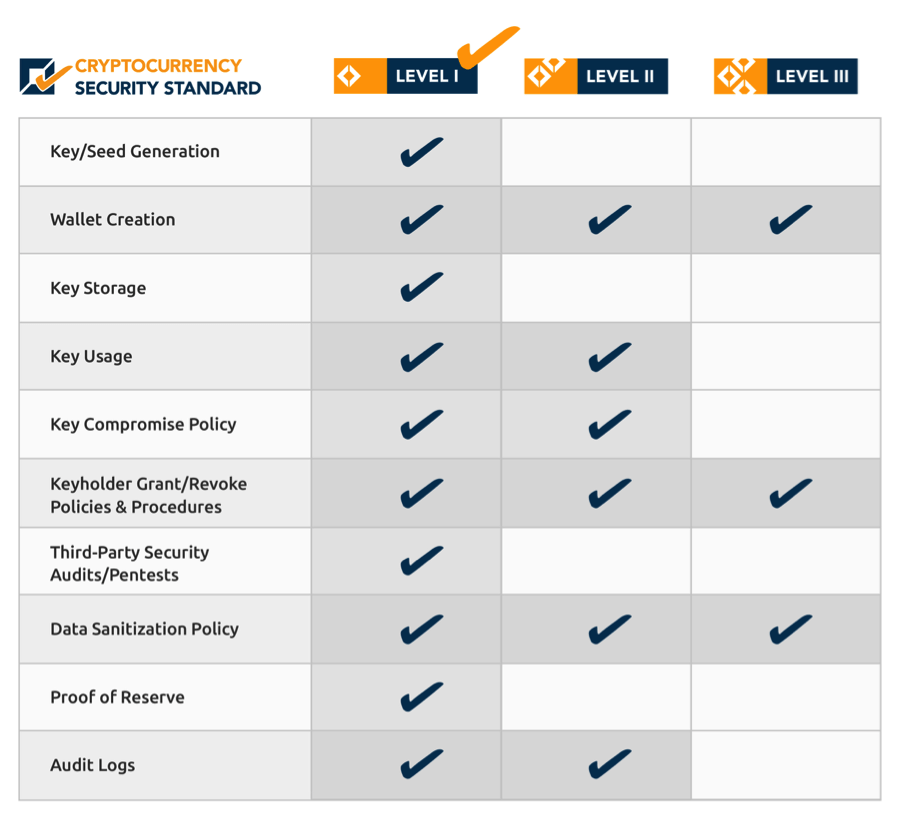
Image source: https://cryptoconsortium.github.io/CCSS/
Becoming CCSS certified shows crypto traders that your business handles their money properly and securely. Use a trusted company like RSI Security to safely store and transact digital currencies by becoming CCSS compliant.
Training Employees for Data Security
Returning to the metaphor of a sinking ship that aptly describes a business without proper security, the RMS Titanic’s infamous death toll was in part brought about by an untrained crew. According to historian Stephanie Barczewski in her book Titanic: A Night Remembered, “the crew had not been trained adequately in carrying out an evacuation. The officers did not know how many they could safely put aboard the lifeboats and launched many of them barely half-full.”
Companies, recognizing that “crew” working with their company are potential liabilities either out of negligence when protecting data or out of spite. Thus, 60 percent of organizations implemented training and awareness programs (as indicated in the chart below) to help prevent data loss.
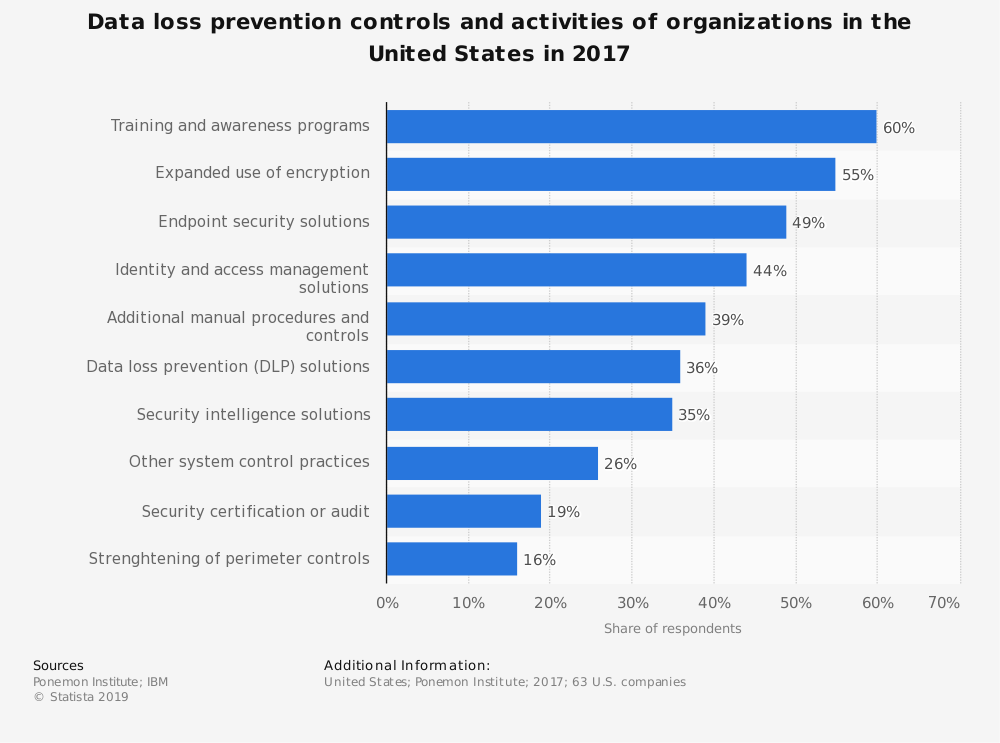
Source, Statista: https://www.statista.com/statistics/437177/data-loss-prevention-us-companies/
Closing Thoughts
A business like a well-run ship reliably serves customers’ needs from maiden voyage and on. Businesses adapt security policies smartly anticipating potential disasters and changing environments. Should a disastrous event occur in which an iceberg of massive proportions cause damage to the ship, then having the proper training and life-saving measures in place are critical to maintaining customer trust.
Working with trusted Cybersecurity companies like RSI Security guarantees that you can focus on the things that make your customers keep coming back again and again while they make sure the ship is in top shape.

