Credit and debit cards have been around since the 1850s, but werent commonplace in American wallets until the 1970s. Why? Because consumers were wary of using them due to the nonexistent security measures and legislative support that was in place at the time. Consumer complaints against this lack of regulation led to the implementation of the Fair Credit Reporting Act of 1970, the Unsolicited Credit Card Act of 1970, the Fair Credit Billing Act of 1974, the Equal Credit Opportunity Act 1974, the Fair Debt Collection Practices Act of 1977. The passing of these acts gave consumers the support and confidence to use their credit and debit cards at a merchant without having to worry about having their data stolen or being discriminated for their transactions.
As time has progressed, hackers have created tools that have given them the ability to access consumer data relatively easily, making data breaches a serious problem for all businesses. To deter the progress of hackers, the PCI Security Standards Council (The Council for short) enacted the universal security standard that is PCI (Payment Card Industry) DSS (Data Security Standard) compliance in December of 2004. The features that The Council has enacted detail a prioritized approach to dealing with their DSS, with six practical milestones that are broken into a smaller subset of relevant controls that will be highlighted later in this article. With more than 898 million records of sensitive information being breached from 4,823 public data breaches that occurred between January 2005 and April 2016, it would behoove your business to be PCI compliant regardless of the number of credit or debit card transactions you process on an annual basis. Knowing what DSS is, what types of DSS there are, and how you can become (and remain) compliant with DSS is critical. Without further ado, here is a DSS breakdown of everything you need to know to protect your business.
What are Data Security Standards (DSS)?
PCI DSS is a set of regulations created by 5 major payment card brands: Visa, MasterCard, American Express, Discover, and JCB. The latest version of PCI DSS (version 3.2) was released in April 2016 with the Council setting these requirements for any business that processes credit or debit card transactions. In a nutshell, DSS requires that your organization is compliant with 12 general data security requirements that include over 200 sub-requirements. The types of requirements and sub-requirement ultimately depend on your business and how many credit card transactions that you perform on a yearly basis. Just checking the PCI DSS compliance boxes isnt the best route to travel if your organization wants to ensure effective protection of every data security situation.
PCI DSS requirements includes practices such as the restriction of cardholder data, the need for creating safe, non-default passwords, and more in-depth practices such as encryption and firewall implementation. Furthermore, DSS provides a means of intrusion detection, sets standards for who can access consumer data, and creates a platform for legally collecting this information. Safeguarding your sensitive data and information by complying with PCI DSS will help your business build long lasting and trusting relationships with your customers.
If your organization is conjuring remote access for administrators, Multi-factor authentication (MFA) is now a requirement. MFA refers to SMS authentication, OTP, thumb, retina, or hand scan technologies. Having multiple factors at the point of access, ensures that only authorized personnel can access appropriate resources. While 86% of consumers say that using MFA makes them feel more secure about the status of their online information it just is one of many security layers that need to be collectively implemented to fully secure your environment to the standards of The Council.
PCI DSS Compliance Overview
After finding that SSL 3.0 was being taken advantage of by the Padding Oracle On Downgraded Legacy Encryption (POODLE) exploit, The Council decreed in PCI DSS version 3.1 that was released in April 2015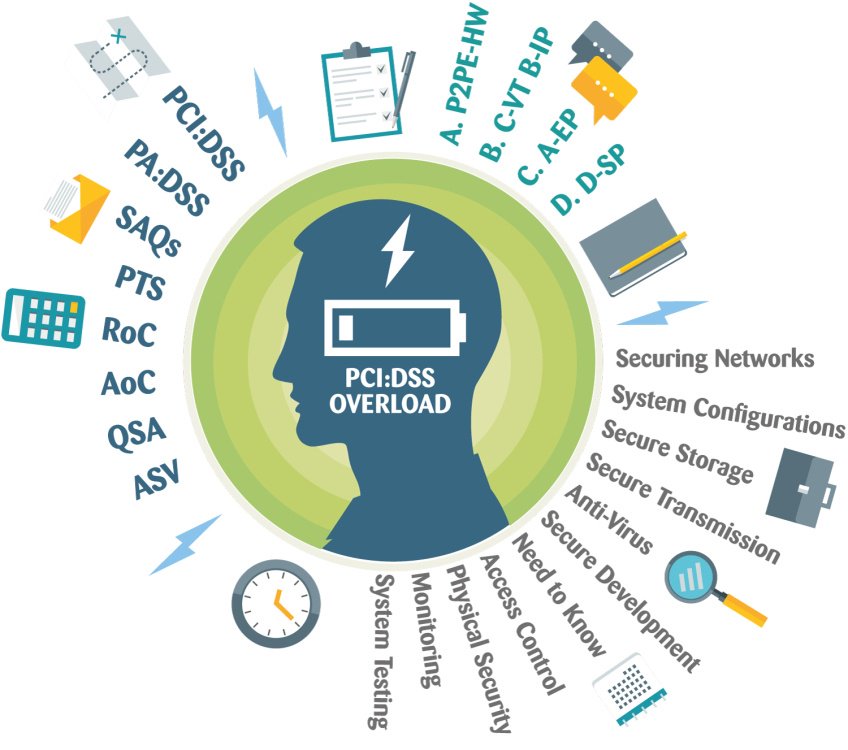 that Secure Sockets Layer (SSL) version 3.0 is no longer considered strong encryption for the transport of cardholder data over public networks or for non-console administrative access to your cardholder data environment (CDE). Early versions of Transport Layer Security (TLS) are essentially upgraded versions of SSL, which means that companies must be updated to TLSv1.2 to make cipher suite negotiations more secure.
that Secure Sockets Layer (SSL) version 3.0 is no longer considered strong encryption for the transport of cardholder data over public networks or for non-console administrative access to your cardholder data environment (CDE). Early versions of Transport Layer Security (TLS) are essentially upgraded versions of SSL, which means that companies must be updated to TLSv1.2 to make cipher suite negotiations more secure.
Basically, if youre still using SSLv3 and early versions of TLS as of June 30, 2018, your CDE wont be compliant with PCI DSS. Noncompliance fines of $5,000 to $500,000 can cripple companies, causing short and long-term customer, supplier, and partner reputations to be damaged. The cost of noncompliance, both in monetary and reputational terms, should be enough to convince any business owner to take data security seriously. Alas, 55% of companies feel that complying with PCI DSS would be a challenging task to accomplish. This might be the case for most companies that are not spending enough on maintaining or meeting compliance, as only 14.3% of the average IT departments budget is allocated for PCI DSS compliance.
PCI DSS Compliance Breakdown
Non-compliance costs 2.71 times the cost of maintaining or meeting compliance requirements. Non-compliance costs are associated with business disruption, productivity losses, fines, penalties, and settlement costs, among others. Staying abreast on PCI DSS compliance is key if you want to keep these CDE disruptions from occurring. The types of DSS that your company needs to be aware of are as follows:
|
PCI Data Security Standard (DSS) Breakdown |
||
| Goals | # | PCI DSS Compliance Requirement |
| Build and Maintain a Secure Network | 1 | Install and maintain a firewall configuration to protect cardholder data. |
| 2 | Do not use vendor-supplied defaults for system passwords and other security parameters. | |
| Protect Cardholder Data | 3 | Protect stored cardholder data. |
| 4 | Encrypt transmission of cardholder data across open, public networks. | |
| Maintain a Vulnerability Management Program | 5 | Protect all systems against malware and regularly update anti-virus software or programs. |
| 6 | Develop and maintain secure systems and applications. | |
| Implement Strong Access Control Measures | 7 | Restrict access to cardholder data by business need-to-know. |
| 8 | Identify and authenticate access to system components. | |
| 9 | Restrict physical access to cardholder data. | |
| Regular Monitor and Test Networks | 10 | Track and monitor all access to network resources and cardholder data. |
| 11 | Regularly test security systems and processes. | |
| Maintain an Information Security Policy | 12 | Maintain a policy that addresses information security for all personnel. |
| Line items 5, 8, and 12 have been updated to correspond with the latest April 2016 changes to the PCI DSS compliance checklist (v3.2) from The PCI Security Standards Council. | ||
Category 1 (Build and Maintain a Secure Network) focuses on the network security of your cardholder data environment (CDE). Your organization must address the creation and maintenance of a network protected from malicious individuals via physical and virtual means. Using hardware and/or software firewall technology can help to provide perimeter protection for a CDE, thus helping to ensure that public information cannot be used by hackers to access your systems.
Category 2 (Protect Cardholder Data) focuses on guidance and testing procedures for data retention, transmission and disposal policies. Basically, this category is a reflection on how your company handles cardholder data (CHD) when it is necessary and how it disposes of said data when it is unnecessary to store it.
Category 3 (Maintain a Vulnerability Management Program) focuses on assessing system and application vulnerabilities (current and future). The Council provides guidance and testing procedures that pertain to malware, software patches, policies and internal procedures for the basis of this category.
Category 4 (Implement Strong Access Control Measures) focuses on limiting availability to authorized persons or applications via the creation of strong security mechanisms. Remaining selective as to who retains PCI administrative access allows your organization to control measures that allow you to achieve security and PCI DSS compliance.
Category 5 (Regular Monitor and Test Networks) is focused on once an organization has implemented system component security measures. Implement security measures in a CDE is just the beginning though. To achieve PCI DSS compliance, these entities must be able to monitor and test system components to ensure that the measures are effective and auditable.
Category 6 (Maintain an Information Security Policy) focuses on the creation and maintenance of policies that protect CHD to ensure confidentiality, integrity, and availability. Through implementing company-wide rules, your organization can protect CHD information and improve workplace security practices.
Scope of PCI DSS
Understanding the scope of DSS allows your organization to employ sufficient security controls and lower your risk of a data breach. If your business is applying controls on systems that go above and beyond what is expected by The Council, it could put more financial stress on your business to maintain these systems. If your resources are already limited for PCI compliance, the addition of more compliance efforts and/or costs resulting from an incorrect assessment scope could spell disaster for your IT department and company. An important prerequisite to reduce the scope of the cardholder data environment is a clear understanding of business needs and processes related to the storage, processing or transmission of cardholder data.
Your organizations CDE is comprised of people, processes and technologies that store, process, or transmit cardholder data or sensitive authentication data. To be considered out of scope for PCI DSS, a system component must be properly segmented from the CDE, such that even if the out-of-scope system component was compromised it could not impact the security of the CDE. Restricting cardholder data to as few locations as possible by elimination of unnecessary data, and consolidation of necessary data, may require reengineering of long-standing business practices.
At least annually and prior to the annual assessment, the assessed entity should confirm the accuracy of their PCI DSS scope by identifying all locations and flows of cardholder data, and identify all systems that are connected to or, if compromised, could impact the CDE to ensure they are included in the PCI DSS scope. If the scope is incorrect and excludes people, processes, systems and networks that may have an impact the security of the CDE, then cardholder data or sensitive authentication data may be insufficiently protected and at risk, thereby making the organizations DSS out of scope.

Which DSS SAQ Best Applies to My Environment?
Self-Assessment Questionnaires (SAQs) are benchmark tests that allow the Council to assess your actual PCI DSS compliance based on the level of your organization. These self-assessments are all about ensuring your organization and clients are as protected as possible from the risk of data breaches and fraud. Failing to get your SAQ right can seriously endanger your business and place customer details at risk, which is why its so important to take SAQs seriously, and complete them correctly.
A one size fits all approach to SAQs is not appropriate because organizations come in all shapes and sizes. Therefore, a range of SAQs has been developed to suit a variety of business types:
| SAQ | Appropriate For | Requirements | # Of Questions | Vulnerability Scan Needed? | Penetration Test Needed? |
| A | Card-not-present merchants (e-Commerce or mail/telephone order) | No electronic storage, processing, or transmission of any cardholder data on the merchants systems or premises. | 22 | No | No |
| A-EP | e-Commerce merchants | No electronic storage, processing, or transmission of any cardholder data on the merchants systems or premises. | 191 | No | Yes |
| B | Brick and mortar or mail/telephone order merchants | No electronic cardholder data transmission, processing, or storage. | 41 | No | No |
| B-IP | Brick and mortar or mail/telephone order merchants | PTS-approved payment terminals with an IP connection to the payment processor, and that have no electronic cardholder data storage. | 82 | No | No |
| C-VT | Brick and mortar or mail/telephone order merchants | Virtual terminal on one computer dedicated solely to card processing. No electronic cardholder data storage. | 79 | Yes | No |
| C | Brick and mortar or mail/telephone order merchants | Payment application connected to the Internet, but with no electronic cardholder data storage. | 160 | Yes | No |
| P2PE | Brick and mortar or mail/telephone order merchants | Must use approved point-to-point encryption (P2PE) devices, with no electronic card data storage. | 33 | No | No |
| D | Merchants and service providers only | No outsourcing of credit card processing or use of a P2PE solution. | 329 | Yes | Yes |
*Any companies that meet PCI compliance Levels 2, 3 or 4 must complete the PCI DSS SAQ annually and undergo quarterly network security scans with an Authorized Scanning Vendor (ASV).
For further understanding of this chart, please reference The Councils PDF guide on PCI DSS version 3 here.
Levels of PCI Compliance
Not sure which SAQ applies to your business? Well, youre in luck, because the Council breaks it down for you in laments terms thanks to this snazzy chart:
| Level | Affected Businesses | Compliance Requirements |
| 1 | More than 6 million transactions annually across all channels including e-commerce. | Annual on-site PCI security assessments and quarterly network scans |
| 2 | 1 million to 5,999,999 transactions annually | Annual security self-assessment and quarterly network scans |
| 3 | 20,000 to 1 million transactions annually | Annual security self-assessment and quarterly network scans |
| 4 | Fewer than 20,000 e-commerce transactions annually and all merchants across channel up to 1 million transactions annually | Annual security self-assessment and quarterly network scans |
Basically, if youre a merchant that processes over $20,000 in transactions annually, you need to be PCI DSS compliant. E-commerce merchants who process, store, or transmit cardholder data are required, by the credit card companies themselves, to have external checks on their network vulnerability by Approved Scanning Vendors (ASV) (Youll find RSI Security on this list of Approved Scanning Vendors).
Closing Thoughts
44% of surveyed companies consider non-compliance fees to damage their brand as an acquirer. Without PCI compliance, agency leaders are putting their clients at risk for data breaches that can jeopardize the private information of millions of customers through their day-by-day operations. PCI DSS compliance, if properly maintained, can certainly contribute to overall security, but it should be viewed as a supplement to already robust, organization-wide security initiatives. By implementing new support technologies such as point-to-point (P2P) encryption, tokenization, and biometrics, your organization can stay ahead of a potential hacker threat and further protect your consumer data.
Contact Us Now!


