Sensitive patient health information is a high-value target for hackers, and the frequency and severity of healthcare data breaches continue to rise. For example, 142 healthcare breaches exposed more than 3.15 million patient records in just the second quarter of 2018. As data breaches increase year over year, it’s critical for medical practices and healthcare organizations to ensure proper protection and handling of personal health information. The Health Information Technology for Economic and Clinical Health Act (HITECH) expanded the reach of HIPAA (Health Insurance Portability and Accountability Act), making HIPAA compliance essential across a broader range of organizations. Whether you operate a healthcare facility or provide related services, understanding and maintaining HIPAA compliance is key to protecting sensitive patient data and avoiding costly violations.
HIPAA in Brief
In 1996, Congress enacted the Health Insurance Portability and Accountability Act (HIPAA) to protect private health information, particularly when individuals change jobs. In 2003, the Department of Health and Human Services introduced the Privacy Rule, which governs how covered entities collect, store, and use Protected Health Information (PHI). This includes information about healthcare provision, current health status, and any healthcare payments linked to individuals.
The HIPAA Security Rule, updated in 2005, placed greater emphasis on electronically stored PHI (ePHI) and introduced three critical categories of safeguards to maintain HIPAA compliance:
- Administrative safeguards: Policies and procedures that demonstrate compliance and ensure proper management of PHI.
- Physical safeguards: Measures to limit or restrict access to areas where PHI is stored.
- Technical safeguards: Security technologies and protocols, such as secure electronic communication channels for transmitting PHI.
Understanding these rules is essential for any healthcare organization or related service provider to maintain HIPAA compliance and protect sensitive patient information.

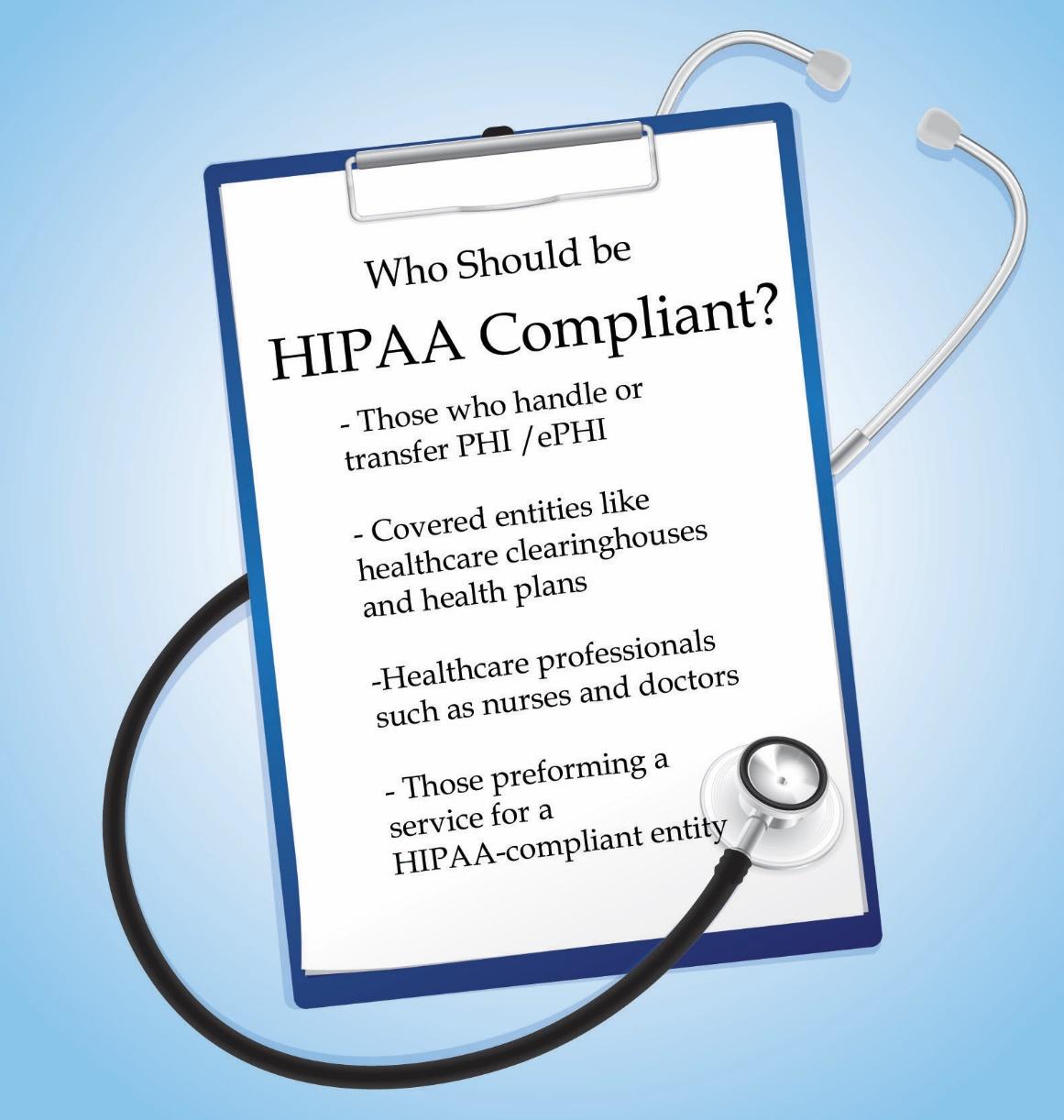
Who Should Maintain HIPAA Compliance?
Any individual or organization that handles, transfers, or accesses PHI (Protected Health Information) and ePHI (electronically protected health information) is required to meet HIPAA compliance standards. This includes covered entities such as healthcare providers, health plans, and healthcare clearinghouses. Healthcare professionals—including doctors, nurses, and IT staff working in regulated environments, must also adhere to HIPAA compliance requirements.
Additionally, the Health Information Technology for Economic and Clinical Health Act (HITECH) extends HIPAA compliance obligations to business associates, any individuals or entities that handle protected health information while providing services.
Organizations beyond traditional healthcare settings must also comply. For instance:
- Audit firms performing work for HIPAA-covered entities.
- SaaS providers that manage healthcare-related data.
- Human resources platforms involved with managing employee health programs.
Ensuring compliance across all relevant personnel and platforms is essential for protecting sensitive health information and avoiding regulatory penalties.
Consequences of HIPAA Non-Compliance
The Department of Health and Human Services (HHS) oversees HIPAA compliance through the Office for Civil Rights (OCR), which is responsible for enforcing the regule HITECH Act and the HIPAA Omnibus Rule fuations within organizations. While the Enforcement Rule was updated between 1996 and 2009, thrther strengthened HIPAA compliance requirements and expanded penalties for violations.
Failing to maintain HIPAA compliance can result in serious consequences, including significant civil fines and, in extreme cases, criminal penalties. Organizations and individuals that mishandle protected health information (PHI) risk reputational damage, financial loss, and legal action.
Why Continuous HIPAA Compliance Monitoring Is Essential
HIPAA requires organizations to conduct regular risk assessments and maintain an ongoing risk analysis process. The Administrative Safeguards provisions reinforce this, mandating that institutions continuously evaluate and manage potential risks to protect sensitive health information. Integrating these assessments into a security and risk management framework strengthens overall organizational security.
The Security Rule outlines management and risk analysis provisions, which help determine appropriate security measures for covered entities. By guiding the implementation of administrative, physical, and technical safeguards, risk analysis plays a critical role in maintaining HIPAA compliance.
Continuous risk analysis is not a one-time task. Regularly reviewing access to ePHI and monitoring for security incidents ensures that organizations can proactively address vulnerabilities. Because malicious actors constantly evolve their methods, ongoing monitoring is essential to protect patient data .
Enabling Risk Management Through a Strong Compliance Program
Effective risk management is a critical component of any cybersecurity framework. Controls can quickly become outdated, and new threats, from previously unknown malware to emerging vulnerabilities, constantly arise. Continuous monitoring helps organizations identify risks that could compromise sensitive patient data, but monitoring alone is just the first step.
Maintaining continuous HIPAA compliance requires addressing risks as they emerge. Covered entities must implement robust policies and procedures to ensure that ePHI is not improperly accessed, altered, destroyed, or damaged. A proactive compliance program strengthens risk management and helps protect both patient information and the organization’s reputation.
Integrating Continuous Audits into HIPAA Risk Management
A security-first approach to cybersecurity not only identifies risks but also mitigates them as they arise. This proactive strategy helps maintain the confidentiality, integrity, and availability of sensitive health information while supporting ongoing HIPAA compliance. Automated tools play a critical role in continuously monitoring potential threats, making them an essential component of any compliance program.
Maintaining HIPAA compliance, especially when partnering with HITRUST-certified vendors, and RSI Security elevates the protection of sensitive patient data. This ensures healthcare organizations can uphold a higher standard of security, safeguard patient trust, and foster a safe and effective healthcare system.
Download Our HIPPA Checklist

