Keeping data centers secure is paramount, but this isn’t always easy for businesses to accomplish. It often depends on the location of the data center, along with the number of devices that can access it. Having access controls in place can improve security in and around data centers, but companies also need to know which ones are necessary.
Blog
-

Guide to Third-Party Risk Management Software
Third-party vendors and suppliers play an important role in a business’s success. As part of the supply chain, whether it’s services or goods, companies rely on their third-party partners. This often results in a chain of connections between the business and supplier that hackers can potentially exploit. A cybersecurity breach can disrupt the supply chain, and also result in non-compliance fines and penalties.
-

Update on PCI DSS 3.2 Password Security Requirements
If your company processes payments using credit cards, you’re required to maintain compliance with standards set out by the Payment Card Industry (PCI) Security Standards Council (SSC).
-

How to Implement Third-Party Risk Management Policies
Businesses rely on their third-party suppliers to deliver products or services on time, while also keeping costs down and improving profitability. However, as beneficial as third-party relationships are to the organization, it does come with risks. These include security breaches and data thefts that often result in non-compliance penalties and loss of consumer trust. Supply chains can also be interrupted.
-

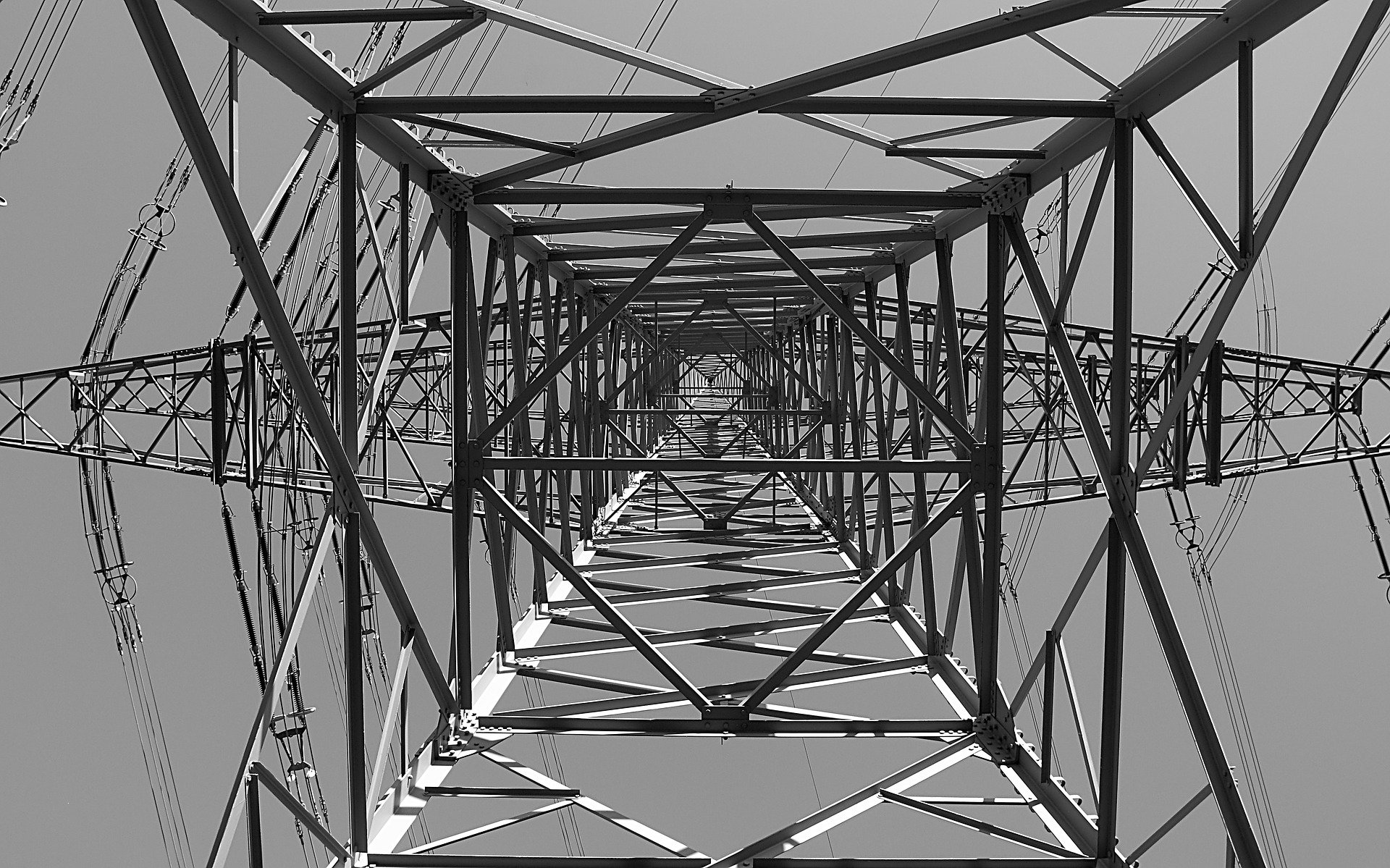
NERC CIP Vulnerability Assessment: A Comprehensive Guide
Safety is of paramount concern when it comes to the bulk electric system of North America. With so many busy cities flourishing on the continent, power interruption will definitely derail the daily grind of its inhabitants and the long-term health of its economies.
-

How to Build an Identity and Access Management Architecture
New technology, an increase in remote employees, and mobile devices have made businesses of all sizes recognize the need for a secure place to store personal protected information (PPI). The data also has to be accessible to those that need it to perform their jobs.
-

What Does a PCI Vulnerability Scan Look For?
All companies that take or otherwise involve payments via credit card expose themselves and their stakeholders to various threats of cybercrime. Cardholder information is some of the most sensitive and valuable data a hacker can get his or her hands on. It enables direct theft of the cardholder’s assets, as well as various other potential fraud or extortion schemes.
-
What Is the Difference Between NERC CIPs and NIST Frameworks?
Essential services such as water, electricity, oil, and gas all require monitoring systems that operate under a communications network. Management of these services becomes more efficient this way. But on the other hand, there is also the potential risk of vulnerability to cyberattacks.
-

How Does Cybersecurity Staff Augmentation Work?
Security staff augmentation is one of the latest solutions to businesses trying to balance tech potential with cybersecurity risk. With each new advance and upgrade, new attack vectors emerge for hackers and malicious intrusions.
-

What is the NIST Zero Trust Architecture?
Many current cybersecurity plans and models follow an older set of priorities that hinge upon the importance of strong perimeter defense. To use a physical analogy many cybersecurity architectures focus on building up the walls and moats protecting the very outside of your castle from attack. But inherent in these schemes is an implicit trust of everyone already inside.
