Essential services such as water, electricity, oil, and gas all require monitoring systems that operate under a communications network. Management of these services becomes more efficient this way. But on the other hand, there is also the potential risk of vulnerability to cyberattacks.
These risks are more than just figments of the imagination. The past years have shown concrete examples of computer hacking, and these have subjected vital aspects of governments to concerns of national security. The United States federal government has created frameworks to address these issues and to improve cybersecurity.
One of these frameworks is the NERC-CIP. The NERC or the North American Electric Reliability Corporation manages the CIP or the Critical Infrastructure Protection standards. This is a set of rules that electric utilities must follow if they are operating bulk power system assets.
Federal entities, on the other hand, must comply with standards from the NIST or the National Institute of Standards and Technology. This is a requirement under the FISMA or Federal Information Security Management Act of 2002.
That’s a lot of terminology and jargon right out of the gate. But hang on, as we will break down everything you need to know about the NERC-CIP and NIST standards.
It can get confusing. These standards refer to uniform engineering or technical methods, practices, and processes for regulation. Several laws in America also impose cybersecurity requirements on utilities. This is why it has been a challenge for many services to determine what is required of them. We provide clarity by discussing the scope, purpose, and perspective of the NERC and NIST cybersecurity standards.
NERC-CIP Standards
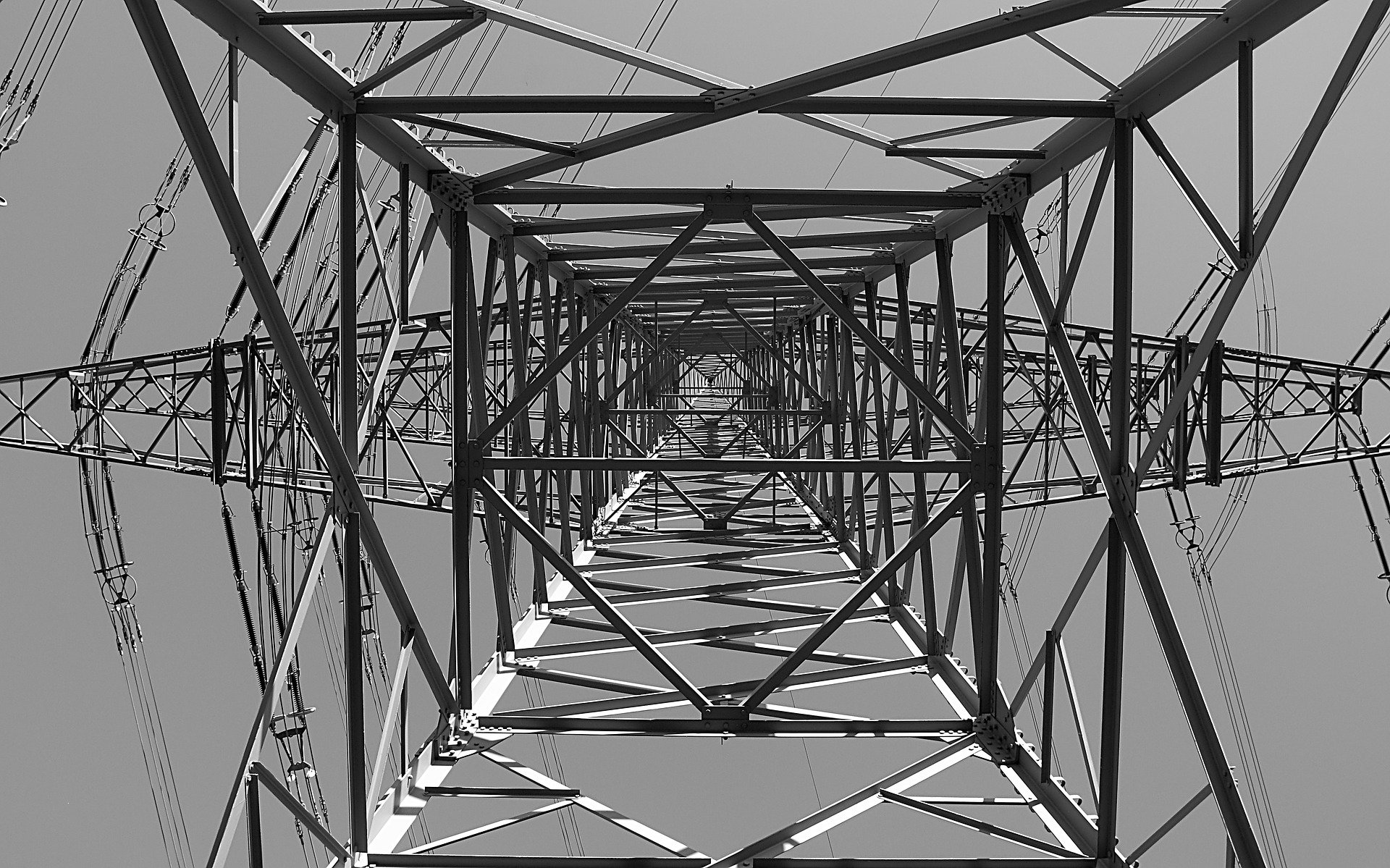
The North American Electric Reliability Corporation or NERC is tasked with overseeing the efficient and effective operation of North America’s bulk electric system. This is a tall order because the entire continent is a vast expanse of highly urbanized and modern cities.
To secure the integrity, safety, and effectiveness of these bulk electric systems, the Federal Energy Regulation Commission or FERC enacted standards called the CIP or Critical Infrastructure Protection.
The CIP standards are composed of 40 rules and 100 sub-requirements. It’s a lot to take in, but all of these guidelines only have one goal in mind: peace of mind when it comes to vital networks that manage our electricity.
Throughout these standards, several essential terminologies are mentioned, including “Critical Assets” and “Responsible Entities.” It’s necessary to understand all these.
Critical Assets comprise the following: data acquisition systems, control systems, networking equipment, virtual storage, and hardware platforms.
As for the Responsible Entities, it includes balancing authorities, reliability coordinators, transmission service providers, transmission owners, generator owners, generator operators, interchange authorities, load serving entities, and regional entities.
These Responsible Entities must follow the guidelines of the NERC. There are several updates to these guidelines because there are numerous digital innovations that bring with it more vulnerabilities. It is essential to always be up to date with all these changes.
These guidelines and standards are collectively called the NERC CIP standards. They were brought about by Order 706 from the FERC in January 2008 and have expanded to accommodate the improvement of technology.

All of the CIP standards are mandatory.
- CIP-002 Cyber Security – BES Cyber System Categorization. This refers to a categorization system that determines which assets are critical when it comes to the bulk electric system of North America. Before enforcing compliance, it is essential to decide on these vital assets. If there is no awareness of how many assets must be protected, there will be room for unforeseen threats.
- CIP-003 Cyber Security – Security Management Controls. This is an outline of controls for configuring and overseeing security. Organizations are mandated to list all the controls they have in place to secure their assets. This is information that is vital to CISOs and cybersecurity program managers. It gives a clear perspective on the existing security steps of the organization.
- CIP-004 Cyber Security – Personnel & Training. Human error is a very unpredictable aspect of cybersecurity. This is why standards for personnel training is essential to make sure they are compliant with the standards of CIP.
- CIP-005 Cyber Security – Electronic Security Parameters. There must be various levels of clearance when it comes to access to the assets. If everyone can just access them, many vulnerabilities may open up. This set of guidelines ensures a clear protocol about who has access to what assets and what degree of clearance they have.
- CIP-006 Cyber Security – Physical Security of BES Cyber Systems. Apart from the electronic access by way of restrictions and passwords, organizations must also take into account the security of the physical location of these assets.
- CIP-007 Cyber Security – System Security Management. Documentation is vital. This makes it easier to monitor any changes or any significant upgrades or untoward incidents within the system. This set of guidelines is focused on information about the management of system security.
- CIP-008 Cyber Security – Incident Reporting and Response Planning. Anticipating a cyber attack is one thing. Your response when it does happen is another. This set of guidelines provides organizations with a documented plan in place when it happens. This includes the organization’s immediate response after the incident, how to report it to authorities, and how to accomplish recovery plans to minimize damage.
- CIP-009 Cyber Security – Recovery Plans for BES Cyber Systems. Foresight is crucial in safeguarding bulk power systems. Suppose there has been damage done in the face of a cyberattack. An organization must also have a documented plan to recover from such a disaster. There must be minimal or zero interruption, even with such an incident.
- CIP-010 Cyber Security – Configuration Change Management and Vulnerability Assessments. This set of guidelines is essential just in case there are unauthorized or unsupervised changes within the bulk power system. This is a contingency in case there is a breach in the first lines of defense.
- CIP-011 Cyber Security – Security Protection. This set of guidelines is created to protect vital information and critical assets of the organization.
- CIP-014 Physical Security. Taking care of vital data is a critical step, but so is the protection of the actual infrastructure. Organizations must protect these physical installations to ensure the reliability and stability of the vital data.
Other CIP guidelines will be enforced shortly. These are all planned and accomplished to strengthen the security of the electric grid and to minimize vulnerabilities. Think of it as a timely update to your favorite smartphone app to ensure that its performance will keep up with its demands.
NIST Standards
The electric power industry has to also comply with another vital United States law that aims to protect bulk electricity systems. This is the FISMA or the Federal Security Management Act of 2002. The focus of this law is to secure federal computer systems under a comprehensive framework of requirements and regulations.
The oversight for this law is the US Office of Management and Budget.
It is not enough to merely comply with the NERC CIP standards. Federal entities that operate and own electric power systems must make sure their control and office systems comply with the NIST standards.
Two documents are essential for compliance under NIST. The first one is the FIPS or the Federal Information Processing Standard. An example is the FIPS-200 that discusses minimum security requirements for federal information systems.
The second type is the NIST Special Publication series. An example is the NIST SP 800-53 that applies to computer systems. This is closer to a framework meant to guide federal entities similar to how NERC-CIP guides to bulk electric power systems.
Together, the FIPS and the SP documents are the foundation for a federal entity to have comprehensive risk management for cybersecurity.
For NIST standards to be integrated within the information system security, an organization must accomplish the following:
- Identification and sorting of systems that require cybersecurity
- Ensuring the confidentiality, availability, and integrity of vital information
- Installing security controls or measures for the system.
The Energy Independence and Security Act of 2007 (EISA) gave more responsibility to NIST in enabling Smart grids. This law mandated NIST to identify which electric utilities may be affected by the shift to a smart grid system. This technology uses more digital information and technology for a more reliable, efficient, and secure electric grid.

The understanding is that smart grids can have better protection against cyber-security threats and terrorism.
Along with other agencies, the shift towards a smart grid system is encapsulated in the NISTIR or the NIST Interagency Report 7628: Smart Grid Cyber Security Requirements. This output will also include NERC CIP standards as one of its guiding principles.
One of the priorities of the NISTIR is the interface or the communications links between systems and devices — not necessarily entire systems. This has strengths and weaknesses.
The advantage is that the NISTIR focuses on making smart grids smarter with the amplified use of monitoring date and real-time control.
The disadvantage is that it may be challenging to apply in some situations — especially if it will be using smart mobile devices. Because the technology is new and growing, it may encounter new vulnerabilities in the future that must be addressed later on.
Tale of the Tape: NERC CIPs vs. NIST
Both the NERC CIP and NIST standards are concerned with the overall safety of communication systems that oversee critical electric assets. It can get confusing as organizations try to decide what to prioritize. But some nuances will help with easier guidance and understanding.
The NERC CIP standards are consensus-based guidelines that must get the approval of the majority before it gets rolled out. The NIST standards do not need to conform to the consensus-based process, and they can merely provide the public with the notice and guidance of the regulations. In principle, NIST gets the feedback of involved agencies for inputs, but there are no specific obligations to respond to these inputs.
This difference is significant because, in the realm of technology, constant feedback, checks, and assessments are needed to see new vulnerabilities, potential problems, and other contingencies. With the consensus-based process of the NERC CIP, it is required to have a comprehensive discussion of the issues with the stakeholders before any change can be enacted. As far as the NIST is concerned, trusted leadership can manage the changes that happen in communication systems.
Both standards are mandated by law, but the NIST is concerned explicitly with federal agencies only. Non-federal agencies can adhere to the guidelines of the NIST but not as a required regulation.
The NIST has been given more responsibilities and has focused its energy on the implementation and management of smart grid systems. Because the smart grid uses newer and more advanced technology, it integrates more security guidelines into the fold. The NIST also uses the NERC CIP as one of its standards, among many others, in this inter-agency cooperation.
The NERC CIP standards are concerned with securing these vital information and communication systems, from training personnel, identifying security controls, security access, the contingencies in the event of a threat, and the protection of critical infrastructure. On the other hand, the NIST has been focusing more on interfaces, or the link between systems and devices to manage these smart grids.
Learn More About NERC CIP and NIST with RSI Security
Mastering the guidelines of NERC CIP and NIST is an essential aspect of responsible entities that operate the bulk power systems that power North America. It may appear complicated and confusing, but you can rely on the experience and expertise of security professionals such as RSI Security to walk you through all these requirements.
Complete compliance with these guidelines will help ensure that there are no vulnerabilities or problems that the bulk power system may encounter. Trust that RSI Security will help you cover all these requirements with maximum efficiency and assistance.