Making the choice for an approved scanning vendor (ASV) is an important consideration for organizations looking to achieve or maintain compliance with the Payment Card Industry (PCI) requirements. The requirements set forth in the PCI Data Security Standards (PCI DSS) are intended to provide end-to-end security for cardholder data. A central component of the PCI DSS is the requirement for entities covered by the PCI DSS to have regular external scans of their networks and systems. As such, PCI approved scanning vendors occupy a central role in ensuring that organizations covered by PCI DSS achieve and maintain compliance advisory services with these requirements over time.
Blog
-

What are the PCI ASV Scanning Requirements?
The process of understanding the entirety of what Payment Card Industry Data Security Standards (PCI DSS) covers is an extremely daunting task for business decision makers. An increasingly important aspect of Payment Card Industry (PCI) compliance has become maintaining compliance with the Approved Scanning Vendor (ASV) requirements notated within PCI DSS. One of the notable requirements that entities must adhere to are those that cover ASV Scans. These vulnerability scans are quite complex in nature and require many man hours of preparation on the vendor and company side to ensure proper consumer payment card protection in the organization’s cardholder environment.
-
ASV Scanning Responsibilities
You have determined that you need vulnerability scanning from an approved scanning vendor (ASV), probably because you need to maintain or establish PCI compliance. Most businesses require at least quarterly scanning. You have done your research and selected a vendor, verified they are approved on the PCI website and are ready to get started. There are several parties involved in this process from the Card Brands to the merchant and the ASV. We will discuss the responsibilities of each.
-

Overview of the FISMA Certification and Accreditation Process
Source: Kaspersky Lab Daily When your grandparents used to lament about security or warn you to lock your doors at night that was as far as the concept of “security” went. No one thought an intruder could penetrate a location without physically breaking down doors. Yet today, bank robbers can steal millions of dollars from the comfort of a desk chair. On a household level, this unauthorized accessibility sounds concerning, but when considered by government agencies, the threat is terrifying. While average households possess a small amount of valuable information, governments store millions of records, usually of a sensitive nature. Realizing the potential implications of remote threats, the U.S. Government developed a set of cyber security guidelines called the Federal Information Security Management Act (FISMA). Are you looking to achieve FISMA compliance? Continue reading for an overview of the FISMA certification and accreditation process.
-

The Three Levels Of Compliance For FISMA
The Federal Information Security Act (FISMA) was introduced in 2002 to ensure that all government vendors, contractors, and partners handle confidential and sensitive information appropriately, intending to provide protection against various security threats. Depending on the nature of your business, you’re going to need to reach specific levels of compliance to avoid FISMA fines, penalties, and consequences.
-

Penalties for Non-Compliance with FISMA (and how to avoid them)
No organization takes cyber security and digital privacy as seriously as the U.S. Department of Defense. It’s why the Federal Information Security Management Act (FISMA) was implemented by the DoD, setting data security standards government partners and contractors. Vendors that fail to comply with FISMA could be in for stiff fines and penalties.
-

Benefits of Being FISMA Compliant
Maintaining compliance with the Federal Information Security Management Act (FISMA) is essential for government agencies or private contractors that deal with those agencies. Since its formal adoption in 2003, FISMA has helped safeguard critical systems and information. Although FISMA compliance is mandatory for some, it carries with it a number of tangible benefits. In this article, we’ll break down what FISMA is, what the requirements of FISMA are, FISMA standards, and what benefits compliance with FISMA brings for covered entities. This information can help inform organizational decisions regarding whether obtaining, or maintaining, FISMA compliance can be beneficial to your organization and its cybersecurity solutions.
-

What Is A FISMA Audit?
In 2002, the internet was ten years old but still in many ways was in its nascent stages. However, its growth had spurred the dissemination and sharing of information at a torrid rate. At the turn of the century, the term “cybersecurity” had yet to become part of the mainstream lexicon. Despite the lack of sophistication in the early days of the internet, the government realized the potential risk that digital information could pose in the wrong hands.
-

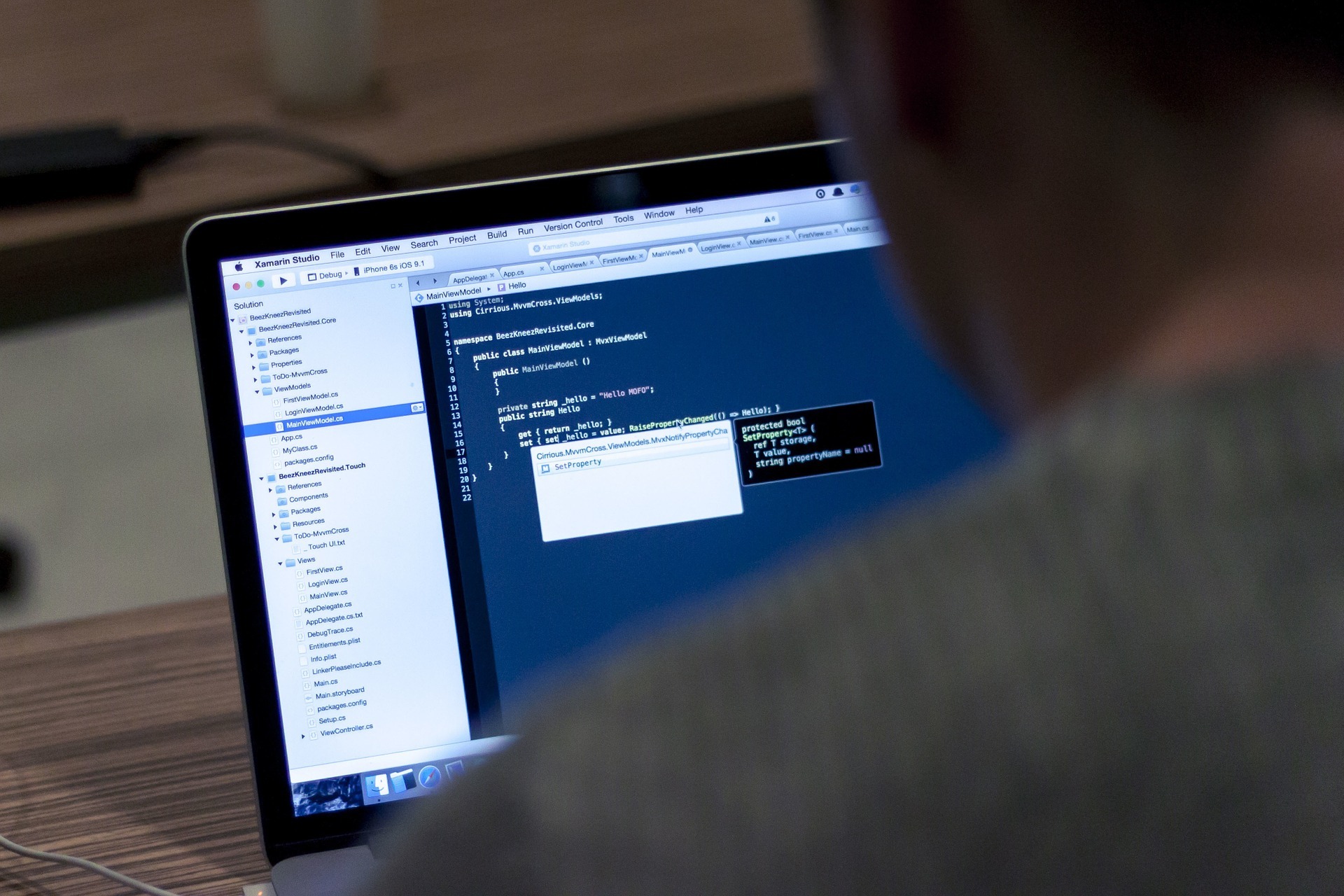
How Does an External Penetration Test Work?
No matter what business you’re in, one of the most important (and worrisome) aspects from a technology standpoint is keeping your data secure. Not to mention that of your customers. But the unfortunate reality is that hackers are working day and night to break into systems and gain access to valuable financial, health, or intellectual property-related data. The question is, how do you figure out where (and how) they might get into your systems, so you can set up barricades ahead of any cyber attack?
-

What Are The Steps To Conducting An Internal Pen Test?
Sometimes the best defense is a good offense. To first do this, you need to think the way the offense of the other team thinks. In cybersecurity, this is done via penetration (pen) testing which serves the purpose of finding network flaws that could potentially be exploited by attackers sometime in the future. One statistic that is constantly quoted is how there is a hacker attack every 39 seconds in the U.S. alone. The one thing about this statistic is that it is over 11 years old. This makes you rethink its current validity and how much more often a hacker attack happens now in comparison to 2007. Considering that today’s complex cyber security landscape harbors emerging threats on a regular basis, we must face the fact that we encounter a plethora of more vulnerabilities than ever before.
