One of the primary goals of cyberdefense programs is identifying, preventing, and mitigating attacks. The best way to do this is with targeted programs, such as penetration and intrusion testing, where attackers’ offensive tactics become your company’s defensive training. (more…)
Blog
-

Major Components of the HITECH Act: What You Should Know
Patients’ medical records are some of the most attractive targets for theft. The US Department of Health and Human Services (HHS) designated them as protected health information (PHI) in the Health Insurance Portability and Accountability Act of 1996 (HIPAA) and laid out measures to ensure their safety. Later, the HITECH Act of 2009 updated these safeguards for the modern era. But what are the major components of the HITECH Act? (more…)
-
Guide to Penetration Assessments and Regulatory Compliance
Some regulatory frameworks explicitly require penetration testing from eligible parties. But even those that don’t require it outright may still have other mandates that would be met or exceeded efficiently by conducting penetration testing. Thus, penetration assessments are critical for your security infrastructure. (more…)
-

Offline vs Online Penetration Testing: Which is Better?
For organizations looking to begin penetration testing, two available options include online (automated) and offline (manual) tests. While automating allows for more frequent and faster testing, manual testing has its own unique benefits in the form of customization and trust. (more…)
-

What is the PCI Security Standards Council?
In the world of financial transactions, the acronym PCI is the most common term used and refers to the Payment Card Industry. (The longer version is PCI DSS, or Payment Card Industry Data Security Standard.) The Payment Card Industry Security Standards Council (PCI SSC) was created in 2006.
Its goal as a global entity is to help improve the security for every aspect of the financial transaction process. In the past the object for security concerns were mainframe computers that could fill a room. Technology has evolved from those huge mainframes to personal computers, to mobile devices such as smartphones and tablets.
The ways hackers threaten an entity’s data have changed as well; but of course, the need for protecting that data has remained unchanged. Keep reading to learn more about the PCI security council and avoiding a credit card data breach.
-
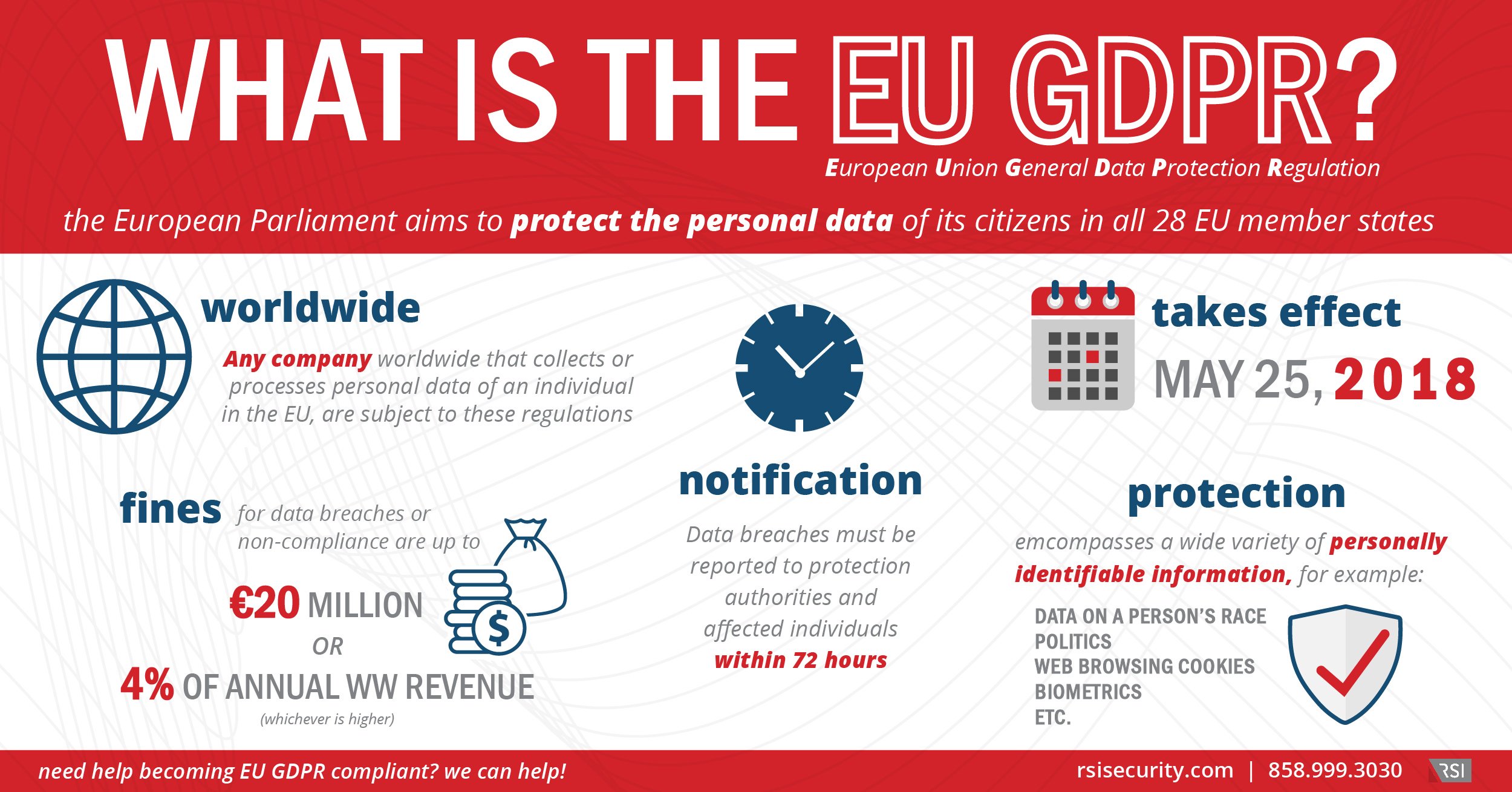
EU GDPR Explained
The impending European Union General Data Protection Regulation (GDPR) represents a sea-change in a company’s security strategies, transcending checkbox compliance programs.
-

How to Conduct Powerful Website Penetration Testing
Looking to pen test your website? Follow this five-step plan for a successful exercise:
- Prepare your defenses to ensure simulated attacks provide the deepest insights
- Negotiate with the testing team to establish scope, targets, and starting positions
- Gather information on your website and web assets to facilitate simulated attacks
- Conduct the agreed-upon penetration testing techniques and escalate, as needed
- Report on findings and use results to optimize defenses, training, and compliance
-

How to Achieve Cryptocurrency Security Standard (CCSS) Compliance
Without a doubt, Bitcoin, cryptocurrency, and the blockchain are in the process of revolutionizing the entire landscape of global finance. Experts from major think tanks like the MIT Technology Review are predicting that cryptocurrency growth isn’t expected to slow anytime soon. As the cryptocurrency industry becomes more prevalent in various aspects of our personal and business lives, so is the need for regulatory standards to ensure transactions take place in a safe, secure manner. Which is exactly why the Cryptocurrency Security Standard (CCSS) was developed.
-

Tailored Social Engineering
What compels your click?
By now most of us recognize obvious spam emails that invite you to view celebrity gossip news or lure you in via offers of free travel or apps. We know that these sites are just a path to disappointment and headache, with quick clicks that lead your PC down an internet dark alley toward viruses or ransomware.
-

Understanding the Role of Risk Control in Risk Management
In cybersecurity terms, a “risk” represents how much harm a threat or vulnerability can cause to your personnel, clientele, and other stakeholders. The role of risk control in risk management is to proactively prevent and mitigate these threats, keeping an organization secure. (more…)
