In today’s world, data security is a central concern for organizations of any size. With attacks happening more frequently and with greater sophistication, organizations must take an increasingly aggressive stance towards protecting their cyber networks and assets against unauthorized access. At the forefront of this effort to combat new and emerging threats has grown a reliance on the tools and best practices utilized to protect enterprise systems from attacks that originate both externally and internally.
Blog
-

PCI Cloud Computing Protections 101
The PCI DSS cloud framework helps organizations protect cardholder data (CHD) stored or processed in cloud environments. Businesses that handle payment data in the cloud must implement strong security controls to defend against evolving cyber threats. By following PCI DSS requirements, your organization can reduce risks, ensure compliance, and maintain trust with customers.
Read on to learn how PCI DSS compliance works and what protections apply to your cloud-based systems. (more…)
-

Cybersecurity Gap Assessment 101
Cybersecurity gap assessments are critical to evaluating the effectiveness of the security controls you implement, ensuring your organization remains protected from threats throughout the year. So what is a gap assessment, and how can it help you optimize your security posture? Read our blog to learn more about these assessments.
What is Cybersecurity Gap Assessment?
Cybersecurity gap assessments enable your organization to systematically evaluate security risks before they can materialize into full-blown threats. To briefly explore the ins and outs of conducting gap assessments, this blog will cover:
- An overview of cybersecurity gap assessments
- How to perform a gap analysis across your assets
- Examples of cybersecurity gap assessments
With the help of a managed security services provider (MSSP), your organization will effectively conduct cybersecurity gap assessments to protect your sensitive digital assets in the short and long term.
What is a Gap Assessment?
A cybersecurity gap assessment is a tool your organization can use to identify weaknesses and vulnerabilities within its cybersecurity infrastructure. Conducting these assessments is critical to promptly discovering these gaps before they can develop into full-blown, high-impact threats.
If your organization handles sensitive data, you will likely need to conduct frequent gap assessments to uncover vulnerabilities that might pose risks to these data.
Compliance with regulatory frameworks like the Payment Card Industry (PCI) Data Security Standards (DSS) and SOC 2 requires gap assessments to address potential data security risks early in their lifecycle. As with any other assessment, you must fully understand why you are doing it and how best to approach it without impacting your organization’s operations.
Request a Free ConsultationHow to Conduct an Effective Gap Assessment
In general, the approach for conducting gap assessments is similar across regulatory frameworks. However, each cybersecurity gap assessment will likely look different, depending on the type of data you handle or your industry. Many of these gap assessment requirements are adapted from the NIST Cybersecurity Framework (CSF), providing industry-standard guidelines for uncovering security gaps and vulnerabilities that can impact data sensitivity.
To provide additional context for how to conduct gap assessments, we’ll review examples of gap analysis from the PCI DSS and SOC 2 compliance requirements.

PCI DSS Gap Assessments
PCI DSS gap assessments are based on the framework’s 12 Requirements, which protect cardholder data (CHD) at rest and in transit. Taking the example of a PCI DSS gap assessment requirements, you can conduct a gap analysis by:
- Evaluating system-wide security – It is highly likely that your system components may have vulnerabilities and gaps you haven’t yet identified, but can only discover with a gap analysis. By evaluating these components across your organization, you can identify gaps like:
- Networks with poorly configured firewalls
- Web application vulnerabilities (e.g., broken access controls)
- Poor cryptographic algorithms
- Assessing sensitive data safeguards – It is also crucial to verify that the safeguards currently protecting your sensitive data are functioning effectively and remain up-to-date with industry standards. Gaps to look out for include:
- Excessive collection or storage of sensitive data
- The unsecured flow of potentially malicious traffic into sensitive data environments
- Evaluating risk management – Risks may include threats, vulnerabilities, and other security gaps, which, if left unaddressed, can result in cyberattacks and data breaches. A thorough review of your existing risk management processes will help:
- Identify ineffective malware or anti-phishing software
- Pinpoint gaps in identity and access management
- Reviewing your security policy – Regardless of industry, every organization needs a security policy to oversee the implementation of cybersecurity controls. Gaps in your organization’s security policy will likely minimize control effectiveness across assets. These gaps may include:
- Improper communication of security objectives
- Ineffective delegation of roles and responsibilities
Although the PCI DSS gap assessment requirements apply to organizations that handle CHD, they provide a general sense of how to conduct these assessments if your organization handles highly sensitive data.
SOC 2 Gap Assessments
For service organizations required to report on System and Organization Controls (SOC), gap assessments can help identify areas in need of remediation and prepare for compliance audits.
Organizations reporting on their SOC 2 compliance can conduct a gap analysis by:
- Evaluating risk management based on categories such as:
- Organizational risks
- Financial risks
- Legal and reputational risks
- Identifying gaps in business continuity processes such as:
- Absence of sensitive data backups
- Incomplete business continuity planning policies
- Assessing physical and logical security gaps such as:
- Absence of user access logging mechanisms
- Lack of identification and authentication procedures
Conducting cybersecurity gap assessments based on the PCI DSS, SOC 2, or other applicable industry compliance requirements will help your organization remain secure—even as threats evolve. With guidance from an MSSP, you will be well-prepared for these assessments, irrespective of the type of sensitive data you handle.
Optimize Your Cybersecurity Gap Assessments
Conducting cybersecurity gap assessments will help your organization remain safe from various security threats. However, partnering with an experienced MSSP will help you optimize these assessments—helping you safeguard sensitive data throughout the year.
To learn more and get started, contact RSI Security today!
-

The Factors of Multifactor Authentication
Authenticate: To prove or serve to prove to be real, true, or genuine.
Thats how Merriam-Webster defines the word, but how does authentication apply to your computing life?
To access our various banking, retail, library, mortgage, etc accounts, we need to first authenticate our identity / credentials, to prove that the person signing in is the account holder or an authorized proxy.
-

Different Types of Hacker Hat Colors Explained

Protecting your critical digital assets from hackers starts with identifying the various types of hackers and how they operate. An understanding of hacker hat colors will help prevent hackers from compromising your IT infrastructure. Read on to learn more about them.
Brief Overview of Hacker Hat Colors
In the cybersecurity world, hackers are known by their hat colors, making it easier to different attacks or attempts thereof by their hacker hat colors. Understanding what each means is essential to creating a robust defense system against all kinds of attacks.
So, below, we’ll explore concepts like:
- The definition of a hacker hat
- The different types of hackers and hacker hats
- The importance of distinguishing between hacker hat colors
With the help of a managed detection and response (MDR) specialist, your organization will be equipped to handle different hacker hats and prevent these attacks from unfolding.
What is a Hacker Hat?
Hacker hat colors simply differentiate between the different types of hackers. Some hackers may be considered “good” (simulated attackers, or testers), whereas others might be described as “bad” (actual attackers). Interestingly, the concept of hacker hats was adapted from Westerns, where movie protagonists and antagonists wore different hat colors.
The Different Types of Hackers & Hacker Hats
When hacker hats were first developed, there were only two hat hacker colors—black and white. As hat hacker behavior has evolved, there are now more colors, pointing to the various types of hacker hat categories in cybersecurity today.
Let’s break these down:
White Hat Hackers
White hat hackers are considered “good” hackers because they are cybersecurity professionals that help organizations uncover security vulnerabilities in their infrastructure. Vulnerability assessment and security testing techniques like penetration testing leverage white hat hacking.
Upon discovering security vulnerabilities during a hacking attempt, these hackers disclose them to organizations at risk of threats or the vendors responsible for the compromised assets.
Request a Free ConsultationGray Hat Hackers
Gray hat hackers are a blend of white and black hat hackers. These hat hackers can be anything from former cybercriminals turned white hat hackers to hackers searching for vulnerabilities in an organization’s infrastructure, without malicious intent.

Black Hat Hackers
Unlike their white hat counterparts, black hat hackers are cybercriminals. They attempt to find vulnerabilities in their targets’ cybersecurity infrastructure. On identifying these vulnerabilities, the black hat hackers may exploit them for monetary gain or espionage purposes.
Green Hat Hackers
Green hat hackers are those interested in becoming seasoned hackers but don’t currently have the hacking knowledge or experience. In a sense, green hat hackers are “wannabe” hackers. When presented with the right opportunity, these hackers could threaten an organization’s cybersecurity, especially when security controls are weak.
Blue Hat Hackers
Somewhat similar to gray hat hackers, blue hat hackers are formally or informally employed by organizations as security consultants. By hiring or outsourcing blue hat hackers, organizations can leverage their hacking expertise to optimize their employers’ security controls.
Red Hat Hackers
Red hat hackers are most often categorized as those who hack systems running on Linux.
Interestingly, red hat hackers are also sometimes classified as “vigilantes” because they tend to aggressively pursue black hat hackers—inflicting damage on their computing resources.

Script Kiddies
The term “script kiddies” was coined to describe inexperienced hackers who are looking for easy targets or victims for their cybercrime attempts. These cybercriminals use existing hacking techniques to deploy their attacks. Script kiddies may also engage in cybercrime for reasons beyond monetary gain (e.g., for adventure, revenge, etc).
There is considerable crossover between this group and green hat hackers.
State or Nation Sponsored Hackers
As the name suggests, state- or nation-sponsored hackers are hired by states or nations to hack specific target systems. These hackers are typically highly trained and experienced cyber professionals, who hack high-value targets like government institutions. Motivations for these attacks may be monetary or espionage-related.
Why it’s Important to Know the Different Types of Hackers
Knowing the different hat hackers will help you stay ahead of threats to your organization.
For instance, black hat hackers can deploy zero-day attacks by exploiting a range of vulnerabilities. Understanding how these hackers operate will help mitigate these attacks from unfolding. And employing the services of white hat, blue hat, or other benevolent “hackers” can help you stay informed of the techniques black hats use (and how to mitigate their risks).
How to Protect Yourself From Hackers
Hackers can exploit any vulnerabilities present in your cybersecurity infrastructure. You can protect your organization from these hackers by implementing a security operations center (SOC). With the help of a SOC, you will be able to detect threats in real-time, comply with regulatory requirements, and optimize your cyber defenses. And, as you grow your threat intelligence tools, your organization will be more secure from hackers.
Even threats like social engineering are preventable when detected early in their lifecycle.
How RSI Can Help
As hackers become more proficient and deploy advanced attacks, it helps your organization to know the different types of hacker hats and how they work. With the help of an MDR partner like RSI Security, you will be prepared to identify potential hacker activity and prevent hackers from deploying threats. Contact RSI Security today to learn more!
Schedule a Free Consultation
-

The Top Programming Languages For Cyber Security
To keep your organization safe from cyber threats, your team will likely require experience with the top programming languages for cybersecurity. A holistic knowledge of which language applies best to specific threat scenarios will help optimize your security posture. Read our blog to learn more about these cybersecurity programming languages.
Guide to the Top Cybersecurity Programming Languages
Security teams experienced in working with top programming languages for cybersecurity are more likely to prevent or mitigate damage from attacks. To that effect, this blog will cover:
- An overview of programming languages
- The best programming languages for cybersecurity
- The importance of programming languages in cybersecurity
- Cybersecurity applications of programming languages
Choosing which programming languages work best within your organization’s cybersecurity infrastructure will help mitigate cyber threats, especially when guided by a threat and vulnerability management partner.
What Are Programming Languages?
Programming languages are sets of instructions that users provide computers to generate desired outputs. They function as tools by which users can translate the code they write into the binary (strings of ones and zeros) that computers can understand.
Programming languages are classified into two main subgroups:
- Low-level languages – These languages are more difficult for humans to read and understand. However, they enable users to quickly and precisely control computer functions.
- High-level languages – Using words (e.g., order, object, class), high-level languages are easier to decipher and program but much slower to translate into the language computers understand.
However, computing has advanced to the point where the difference in processing between low- and high-level languages is negligible, making high-level languages more popular.
Request a Free ConsultationThe Best Programming Languages for Cyber Security
So, what is the best programming language for cyber security? It depends.
Identifying the best programming language for your organization’s security needs will depend on your unique security infrastructure and the security team’s programming experience. Some languages are easy to learn, whereas others are useful in various cybersecurity settings, regardless of industry. Let’s explore some of the most common programming languages:

Java
First released in the mid-90s, Java is one of the most common programming languages for developing small-scale mobile or software applications or large-scale systems. Java is relatively easy to learn, making it a popular option for introductory programming. And, it one of the most useful programming languages to learn because many websites will not function if Java is not installed on a computer trying to access them.
Python
Python is considered one of the most versatile programming languages and can be used for various applications (e.g., web development, network programming, or data analytics).
Its versatility makes it popular for users new to programming.
Many of the cybersecurity tools on the market run on Python because it’s easy to use and can be automated. Learning how to program using Python will help your team promptly detect threats and deploy appropriate counter defenses.
SQL
Structured Query Language (SQL) is the programming language that enables users to update, delete, or edit information in databases. Since it is the most common programming language used to build and maintain relational databases, cybercriminals often use SQL to gain unauthorized access to sensitive data environments.
SQL is also relatively easy to learn. A basic understanding of SQL will enable cybersecurity professionals to mitigate attacks like SQL injection, where strings of malicious code are added to database files.
JavaScript
JavaScript is the programming language that powers websites. Although websites are built on HTML, JavaScript enables them to run external elements (e.g., plug-ins) or track user activity on websites.
These features make JavaScript a powerful tool for cybercrime. Using JavaScript, perpetrators can deploy cross-site scripting attacks to a target website and compromise its security. Luckily, cybersecurity professionals trained in JavaScript programming can easily detect these attacks and develop mitigatory defenses against them.
C/C++
C is one of the oldest programming languages, developed in 1972. In spite of its age, C is popular and versatile—and typically used to maintain UNIX systems. Users who learn to program in C will often find it easier to learn similar programming languages like Java, Python, C++, and C#. Compared to Java and Python, C is much faster.
Although C++ is an extension of C, both programming languages run on a similar syntax. Whereas C is unable to support classes and objects, C++ can do so.
Ruby
Ruby is also a popular programming language described as “beautiful and artful” by its users. It blends aspects of functional and imperative programming, creating a language that is simple outwardly but inwardly complex.
As a flexible language, users can freely edit, add, or redefine Ruby’s syntax. Unlike other programming languages, it is highly portable and can work on UNIX, macOS, Windows, or DOS.
PHP
PHP is also a versatile programming language that works on most operating systems and web servers. Since it is fast and flexible, PHP is typically used for scripting applications for websites and databases. Learning how to program in PHP enables security teams to promptly identify web application threats, especially those embedded within malicious scripts.
PowerShell
According to Microsoft, PowerShell is a programming language comprising a “command-line shell, a scripting language, and a configuration management framework.” These three features make it a robust tool for automating tasks, deploying technologies, and managing frameworks.
Since PowerShell can be used for cybercrime on Windows, Linux, and macOS, cybersecurity teams must know how this programming language works so they can implement effective counter defenses.

Why Programming Languages Are Important for Cybersecurity
Understanding how programming languages for cybersecurity work can help security teams detect various threats to organizations. For instance, web application threats such as SQL injection or cross-site scripting attacks are deployed using languages like SQL and PHP.
Your security team can also use programming languages to conduct threat intelligence monitoring, promptly identifying critical threats before they spread to your entire IT infrastructure.
What Areas of Cybersecurity Require Coding?
Cybersecurity teams with deep, broad coding experience can more effectively mitigate threats that exploit vulnerabilities in web or email application security. Besides baseline coverage, specific programming experience with languages like SQL helps mitigate database security risks. Experience with C and C++ can help discover vulnerabilities in open-source code, which could impact an organization’s data security.
Which is the Most Secure Programming Language?
Defining which programming language is the most secure depends on many factors, the most common being the number of vulnerabilities listed in the Common Weakness Enumeration (CWE) list. A programming language may not be considered secure if the publicly available vulnerability data shows several exploitable vulnerabilities. And ultimately, every language has some vulnerabilities that may have little to no impact on your organization’s security controls.
Although it is difficult to pinpoint the most secure programming language, a threat and vulnerability management partner will help evaluate the specific risks your organization might encounter when using common programming languages.
How RSI Can Help
When choosing programming languages for cybersecurity controls, it helps to identify versatile, easy-to-use, and secure ones that will help mitigate data security threats. Working with our team at RSI Security will help you identify the most useful programming language to meet your unique security needs. Contact RSI Security today to learn more!
FAQs About Cyber Security Programming Languages
What programming language do hackers use?
Whether it’s Python, PHP, or SQL, hackers can use any programming language that offers the best odds for deploying a successful attack. Which they choose depends largely on the kinds of systems or assets they are targeting and the methods of attack they prefer.
Is Python or Java better for cyber security?
Python is easy to learn and can be applied to a range of software development needs, making it a useful cybersecurity tool for securing software applications. However, Java applies more to web development and can help secure websites.
Although both programming languages are great cybersecurity tools, your choice of either Python or Java will depend on the types of assets you’re looking to protect.
Is coding needed for cyber security?
Although coding is not a strict requirement for cybersecurity, security professionals with programming experience will be better equipped to handle threats developed with code.
-

PCI Logging Requirements 2023: Everything You Need to Know
The PCI DSS Requirements mandate organizations that handle cardholder data to log and monitor access to sensitive data environments. Compliance with these PCI logging requirements will help successfully track network and data security in the long term. Read our blog to learn everything you need to know about these requirements. (more…)
-
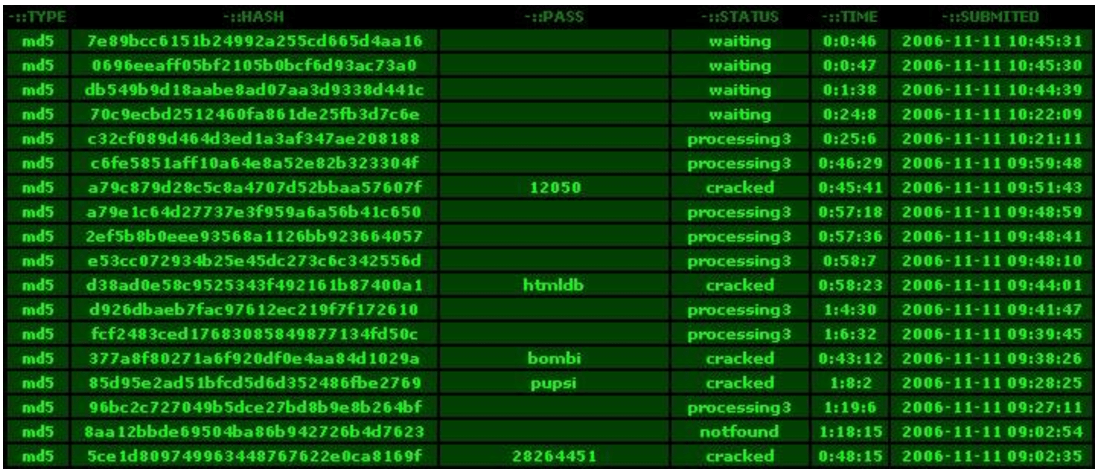
Password Hashing
Following up on our earlier blog on the topic of Password Hacking, here is a deeper technical dive into the process of Password Hashing, and how it helps to keep your passwords secure.
-

Are Apple Computers More Secure Than Windows?
Today, organizations use a mix of Apple and Windows computers, with some leaning towards either type. When looking to acquire or update their computer inventory, organizations ask a common security question: are Apple computers more secure than Windows? Read our blog to learn more about the security of these operating systems—and which might be best for you. (more…)
-

What is Risk Acceptance in Cyber Security?
Cybersecurity risk management is critical to minimizing the impact of risks on data security and safeguarding the integrity of your IT infrastructure. Managing these risks may require risk acceptance, especially for controllable or low-impact risks. Read on to learn more about when and how cybersecurity risk acceptance works.
Cybersecurity Risk Acceptance: A Brief Overview
Understanding how risk acceptance in cyber security works will help you effectively control risks and optimize the security controls you implement across your organization.
So, in this blog, we’ll cover:
- A definition of risk acceptance and how it works
- How to implement risk acceptance
- Why you should implement risk acceptance
Implementing a robust risk management framework will help you mitigate cyber threats and data breach risks, especially in partnership with a threat and vulnerability management specialist.
What is Risk Acceptance?
As the name suggests, risk acceptance means believing that the risks posed by certain threats or vulnerabilities will not significantly impact your assets. A risk acceptance approach accounts for risk management with predefined, existing controls.
For instance, low-impact, constant risks, such as viruses and malware, can be identified and mitigated by controls like firewalls and anti-malware programs. Risk acceptance is one of four common strategies used to control cybersecurity risks.
Other strategies for managing risks include:
- Risk avoidance, where risks are completely avoided (e.g., refraining from collecting sensitive data at risk for privacy and security risks)
- Risk transfer, where risks are passed on to third parties (e.g., outsourcing security to a managed security services provider (MSSP))
- Risk reduction, where risk impact is lowered by implementing processes that the overall likelihood of data being compromised
In cybersecurity, risk acceptance may be implemented along with one or more of the three other risk management strategies.
Risk Retention vs Risk Acceptance: What’s the Difference?
Although risk acceptance and risk retention are somewhat similar, they are different when it comes to the consequences of risks. Retention of risk means that if an organization is impacted by a risk, the organization takes responsibility for the outcomes of not avoiding, transferring, or reducing that risk. Choosing to retain risks also accounts for disruptions to business operations.
Request a Free ConsultationHow the Risk Acceptance Process Works
Before you can accept risks, you must understand what they are and how they can impact your sensitive data environments. You can conduct a risk assessment to identify the risks, evaluate risk level, and then determine whether to invest in risk mitigation or simply accept that risks can be controlled with existing processes.
What is an Acceptable Level of Risk?
An acceptable level of risk is that which will not compromise sensitive data environments and poses minimal risks to your broader information security infrastructure. For instance, installing up-to-date malware blockers or anti-phishing email software on every device connected to your organization’s network means you have reduced malware and phishing threats to an acceptable level of risk. However, it is always best to consult with a threat and vulnerability management partner on recommended acceptable levels of risk for your unique assets.

Implementing a Risk Acceptance Framework
Risk acceptance can be challenging without criteria for when, how, and why risks can be accepted. A risk acceptance framework can provide guidance on best practices for accepting cybersecurity risks. Doing so minimizes guesswork during risk acceptance and streamlines overall risk management.
Risk acceptance frameworks may vary from one organization to another.
Most organizations develop unique risk acceptance and risk management frameworks based on standardized controls recommended by bodies like the National Institutes of Standards and Technology (NIST).
Why Risk Acceptance is Important
Risk acceptance is crucial when it comes to allocating resources to risk management. Some risks are more impactful than others and can cause significant damage to your organization if they develop into threats. In instances where an organization is faced with budget or operational constraints, risk acceptance can be applied to lower-impact risks—freeing up resources to address more pressing, higher-impact risks.
Risk Acceptance Examples
In cybersecurity, acceptable risks may include:
- Keeping legacy systems active if they are not connected to sensitive data environments
- Allowing employees to connect their own devices to an organization’s networks if traffic from these devices is segmented from sensitive networks
Acceptance of risk will likely vary at each organization. Understanding how risk acceptance works in your industry and for your specific needs will help you effectively manage risk in the short and long term.
How RSI Can Help
Implementing risk acceptance within a robust risk management framework will help you maximize your available resources and optimize your security ROI. With the help of an experienced threat and vulnerability management services provider like RSI Security, you can mitigate cybersecurity risks before they develop into full-blown threats.
Contact RSI Security to learn more!