When it comes to data that cyber criminals are after, defense and military information rank near (if not at) the top of the list. And its not something the U.S. Department of Defense (DOD) federal government is taking lightly. Between cyber protection, support, and other teams, the DOD is on pace to have 133 teams of federal agencies dedicated specifically to cyber defense. In addition, the DOD is working with the National Institute of Standards and Technology (NIST) to implement regulations that will also make sensitive data handled by DOD and government contractors secure as well.
Category: Compliance Standards
Staying informed about all of the cyber security compliance standards is essential to keeping your company safe from hackers. Read on to learn about the various steps you can take to stay up to date with your industry’s compliance standards.
-

Major Components of the HITECH Act: What You Should Know
Patients’ medical records are some of the most attractive targets for theft. The US Department of Health and Human Services (HHS) designated them as protected health information (PHI) in the Health Insurance Portability and Accountability Act of 1996 (HIPAA) and laid out measures to ensure their safety. Later, the HITECH Act of 2009 updated these safeguards for the modern era. But what are the major components of the HITECH Act? (more…)
-

What is the PCI Security Standards Council?
In the world of financial transactions, the acronym PCI is the most common term used and refers to the Payment Card Industry. (The longer version is PCI DSS, or Payment Card Industry Data Security Standard.) The Payment Card Industry Security Standards Council (PCI SSC) was created in 2006.
Its goal as a global entity is to help improve the security for every aspect of the financial transaction process. In the past the object for security concerns were mainframe computers that could fill a room. Technology has evolved from those huge mainframes to personal computers, to mobile devices such as smartphones and tablets.
The ways hackers threaten an entity’s data have changed as well; but of course, the need for protecting that data has remained unchanged. Keep reading to learn more about the PCI security council and avoiding a credit card data breach.
-
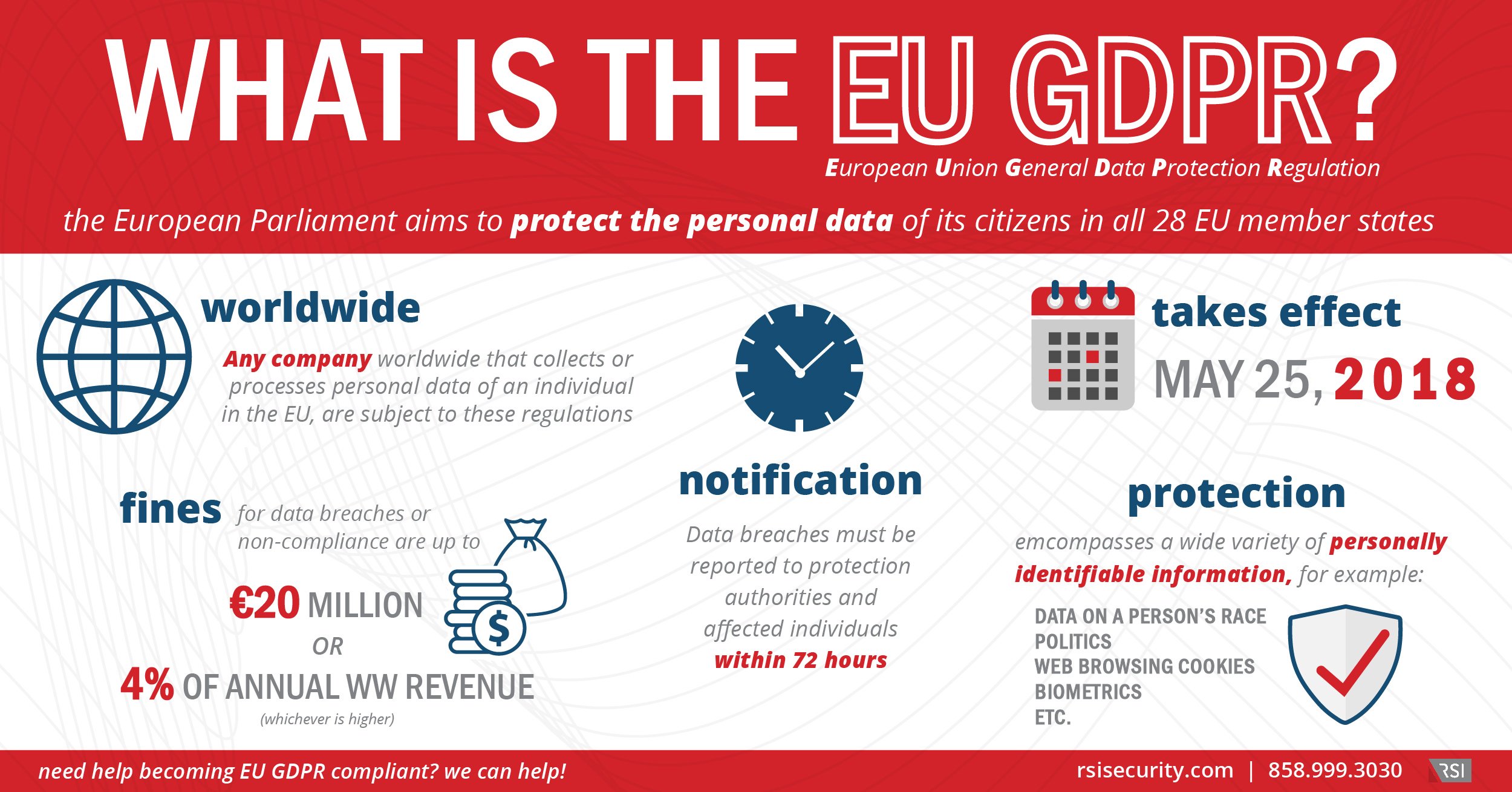
EU GDPR Explained
The impending European Union General Data Protection Regulation (GDPR) represents a sea-change in a company’s security strategies, transcending checkbox compliance programs.
-

How to Achieve Cryptocurrency Security Standard (CCSS) Compliance
Without a doubt, Bitcoin, cryptocurrency, and the blockchain are in the process of revolutionizing the entire landscape of global finance. Experts from major think tanks like the MIT Technology Review are predicting that cryptocurrency growth isn’t expected to slow anytime soon. As the cryptocurrency industry becomes more prevalent in various aspects of our personal and business lives, so is the need for regulatory standards to ensure transactions take place in a safe, secure manner. Which is exactly why the Cryptocurrency Security Standard (CCSS) was developed.
-

How to Achieve PCI Secure SLC Certification Efficiently
If your organization was subject to PA-DSS compliance in years past, you may need to achieve PCI Secure SLC certification as soon as possible. The most efficient path begins with scoping before in-depth implementation and assessment—all of which an advisor can optimize further. (more…)
-

How ASVs Streamline PCI Compliance Scans
If your organization is working toward PCI certification, a PCI vulnerability scan is an essential step. These scans must be performed by a PCI Approved Scanning Vendor (ASV) to meet specific PCI DSS requirements. While ASVs are officially required for external vulnerability testing, trusted providers can also help strengthen your overall compliance program by offering tools and guidance across every stage of implementation.
(more…) -

How to Implement the CIS Controls Framework Efficiently
Organizations looking to install the CIS Controls need to understand the scope of the overall framework, along with the specific practices they need for their target Implementation Group. Then, once all controls are in place, they’ll need to conduct an assessment for verification. (more…)
-

Do You Need to Implement the CIS Critical Security Controls?
Understanding whether you need to implement the CIS security controls comes down to: (more…)
-

PCI DSS 4.0 – Understanding the working of PCI DSS 4.0
In 2019, the Payment Card Industry Security Standards Council (PCI SSC) began taking feedback for improving version 3 (v3.2) of the Payment Card Industry Data Security Standards (PCI DSS). With the new feedback, PCI SSC hopes to publish the final version 4 (v4.0) by 2021. Wondering how PCI DSS 4.0 will work? Get all your questions answered with our comprehensive guide. (more…)
