Updates to the HIPAA Security Rule are expected soon, introducing the most extensive changes in over a decade. These updates will make compliance more complex for covered entities and business associates, increasing the stakes for protecting sensitive health information.
Blog
-

Everything You Need to Do to Prepare for CMMC 2.0 Compliance
Organizations that support the U.S. Department of Defense (DoD) routinely handle sensitive federal data. For these companies, CMMC 2.0 Compliance is not optional, it is a contractual requirement for continued participation in the Defense Industrial Base (DIB).
Preparation requires more than checking boxes. It demands proper scoping, structured implementation, documented evidence, and readiness for formal assessment. Organizations that begin early reduce risk, control costs, and position themselves competitively for future contracts.
If your organization works with Federal Contract Information (FCI) or Controlled Unclassified Information (CUI), now is the time to evaluate your readiness. (more…)
-

Do You Need CMMC Certification? Here’s How to Find Out!
In November 2021, the DoD revised the Cybersecurity Model Maturity Certification (CMMC) program, leading many in the Defense Industrial Base (DIB) to question their compliance needs. The critical issue now is not whether certification is required, but which CMMC level your organization needs to meet.
The nature of the sensitive data you manage will determine the appropriate level and the specific controls you must implement, so addressing this promptly is essential.
-

Why You Need a Cybersecurity Development Program
Cybersecurity program development is the foundation of an organization’s ability to manage risk, maintain regulatory compliance, and protect critical assets. Without a structured security framework, cybersecurity efforts become reactive—driven by incidents rather than strategy.
Many organizations invest in tools, firewalls, and endpoint protection, yet still lack a cohesive cybersecurity program. As a result, security controls operate in silos, risk management lacks executive oversight, and compliance initiatives remain fragmented. Human error, system failures, and evolving cyber threats further compound this exposure.
-
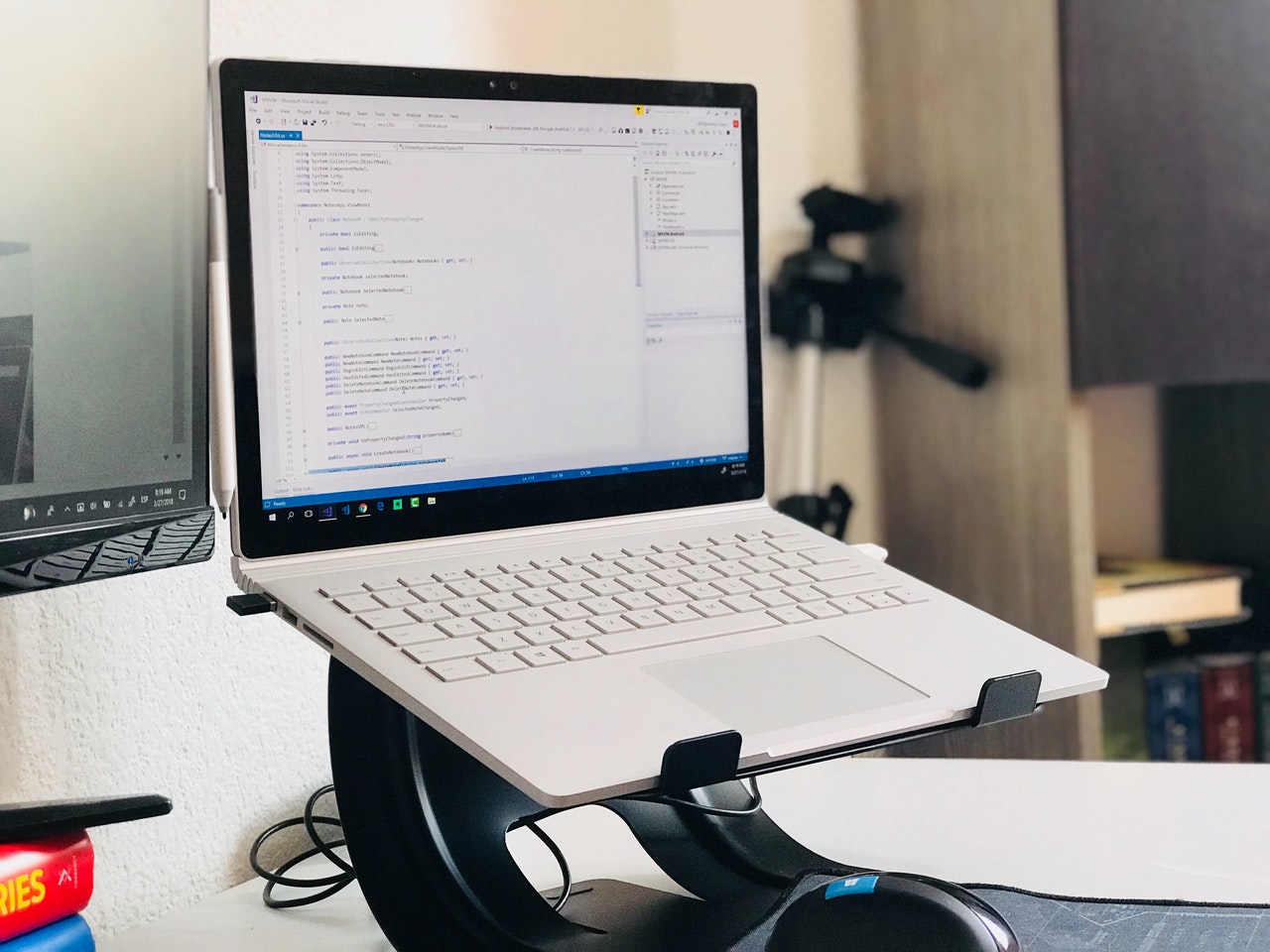
Top CMMC Compliance Software Tools
Companies that want to work with the Department of Defense (DoD) need to ramp up their cybersecurity to protect service members and American citizens worldwide. In practice, this means implementing certified security frameworks like the Cybersecurity Maturity Model Certification (CMMC), published by the Office of the Under Secretary of Defense for Acquisition and Sustainment (OUSD–A&S). CMMC compliance software tools are necessary investments to get started.
-

How to Map NIST Cybersecurity Framework Controls
To work with the US government, organizations need to implement NIST Cybersecurity Framework Controls . NIST SP 800-53 maps CSF principles into executable controls, which then translate into requirements in other frameworks, like SP 800-171, that are required for specific contracts. (more…)
-

Integrating NIST Incident Response and DoD Compliance
Organizations that work with US government agencies have to follow various NIST frameworks to secure sensitive data. NIST incident response is spelled out in NIST SP 800-61, which also informs incident response protocols in other NIST frameworks needed for DoD compliance. (more…)
-
What Are a C3PAO’s Responsibilities in CMMC Compliance?
Cybersecurity within the Defense Industrial Base (DIB) is a matter of national security. That’s why the Department of Defense (DoD) requires contractors to meet strict standards under the Cybersecurity Maturity Model Certification (CMMC). For many organizations, achieving CMMC Level 2 or higher may involve working with a specialized third party: a Certified Third-Party Assessor Organization (C3PAO). But what exactly does a C3PAO do? Let’s break down the critical responsibilities of C3PAOs, and why choosing the right one makes all the difference in your compliance journey. (more…)
-

Artificial Intelligence 2025 Legislation
Artificial intelligence (AI) is transforming every industry, from healthcare and finance to manufacturing and national security. As adoption accelerates, lawmakers are racing to keep pace. New AI legislation in 2025 aims to address growing concerns around privacy, bias, transparency, and accountability.
Organizations that leverage AI must now prepare for stricter AI compliance and regulatory requirements in the U.S. and abroad. Is your business ready for the next wave of AI legislation and enforcement?
Schedule a call to assess your readiness and stay ahead of regulatory changes. -

Why Small Businesses Are More Vulnerable to Security Threats
Small business cybersecurity risks are increasing as threat actors continue to target organizations with limited security resources and oversight. While small businesses face competitive pressure and operational challenges, cybersecurity threats often pose the greatest long-term financial and reputational risk.
Unlike large enterprises, small and mid-sized businesses (SMBs) typically operate without dedicated security teams, continuous monitoring, or formalized risk management programs. This lack of structured cybersecurity governance makes them attractive targets for ransomware, phishing attacks, credential theft, and data breaches.
