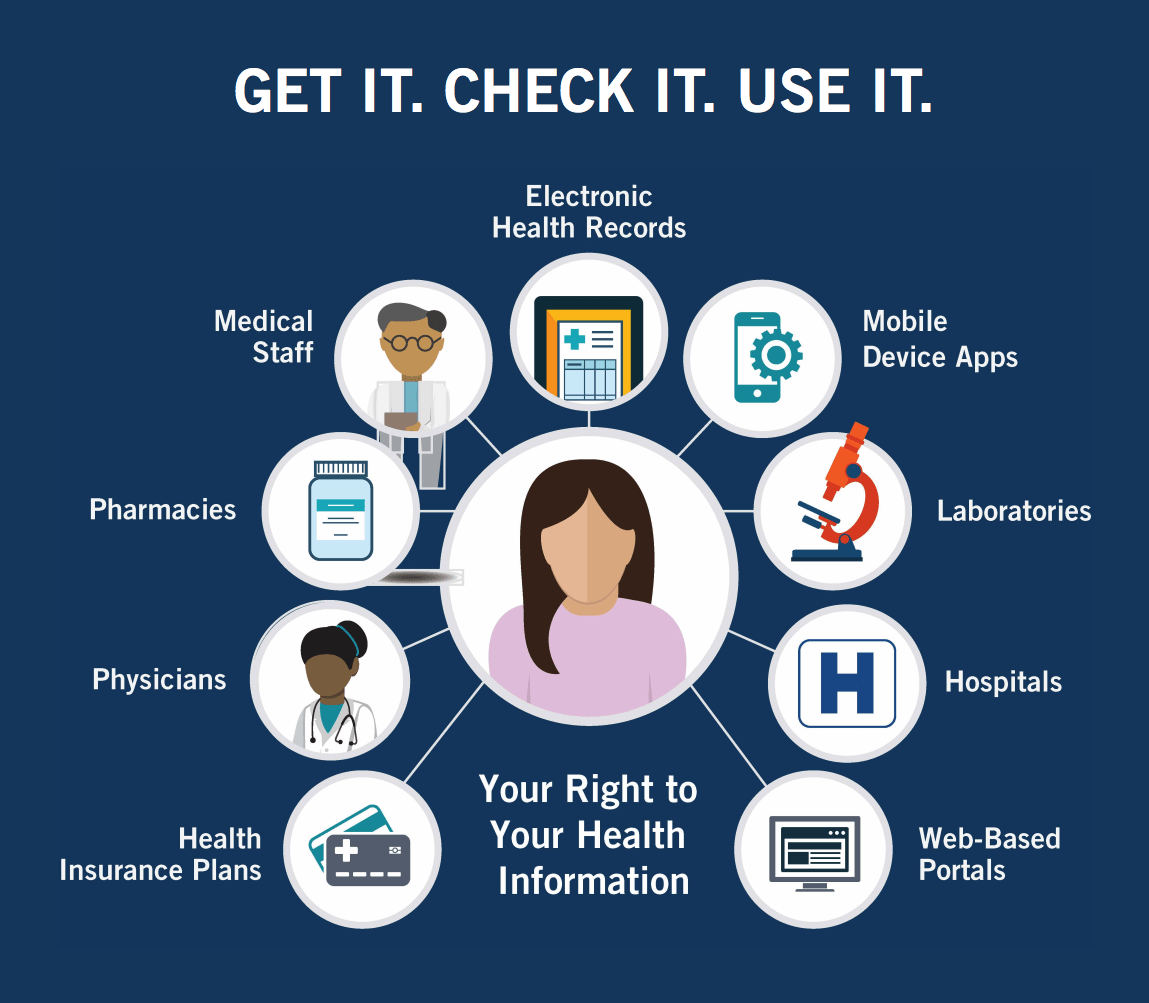
The HIPAA Security Rule outlines specific administrative, physical, and technical safeguards that covered entities must implement to protect electronic protected health information (ePHI). It applies to healthcare providers, health plans, and healthcare clearinghouses that transmit health information electronically.
Under this rule, covered entities are required to conduct regular risk assessments, implement access controls, use secure encryption protocols, and establish ongoing training and monitoring processes to ensure compliance. Failure to meet these requirements can lead to severe penalties, including fines and loss of trust
By adhering to the Security Rule, covered entities reduce the likelihood of breaches and ensure that patient information remains confidential, available, and unaltered—core goals of HIPAA compliance. (more…)