Cybersecurity program development is the foundation of an organization’s ability to manage risk, maintain regulatory compliance, and protect critical assets. Without a structured security framework, cybersecurity efforts become reactive—driven by incidents rather than strategy.
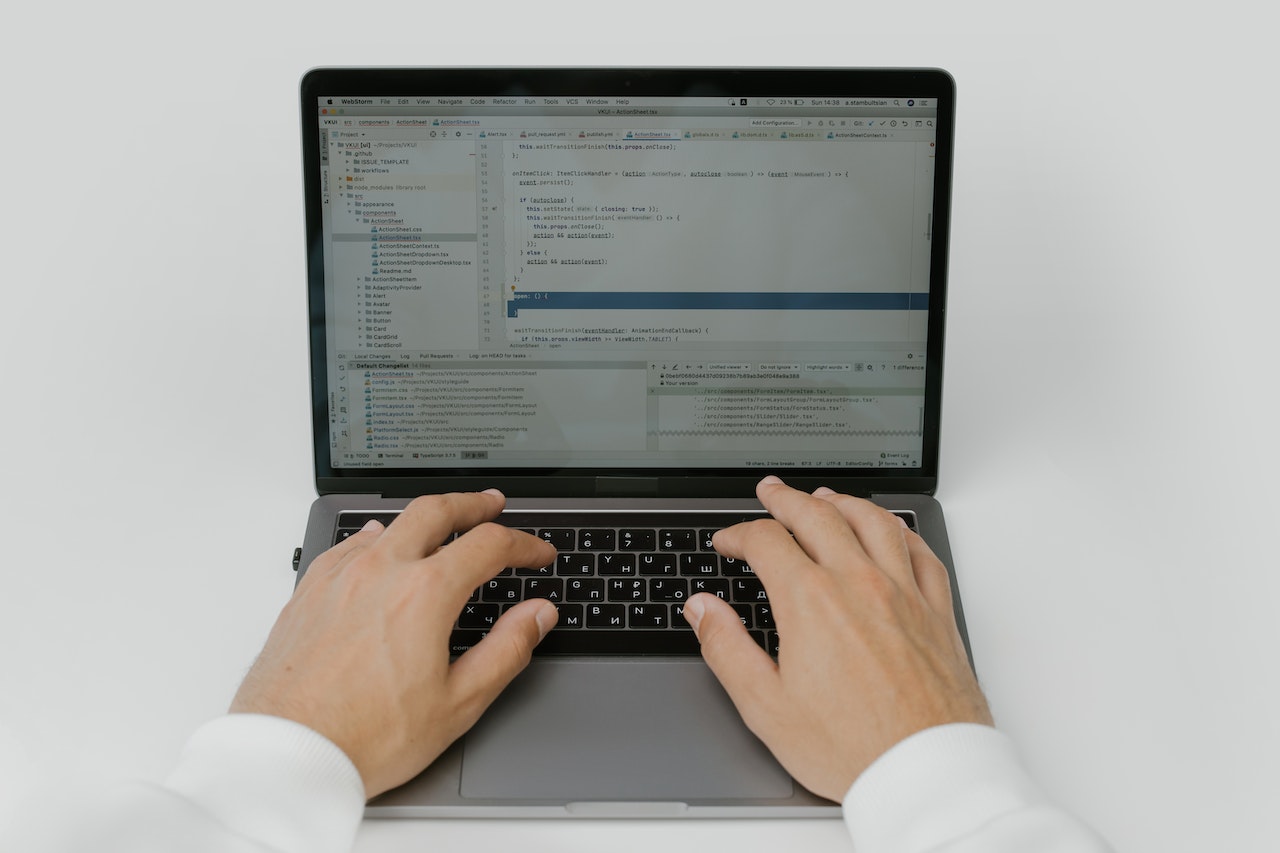
Many organizations invest in tools, firewalls, and endpoint protection, yet still lack a cohesive cybersecurity program. As a result, security controls operate in silos, risk management lacks executive oversight, and compliance initiatives remain fragmented. Human error, system failures, and evolving cyber threats further compound this exposure.