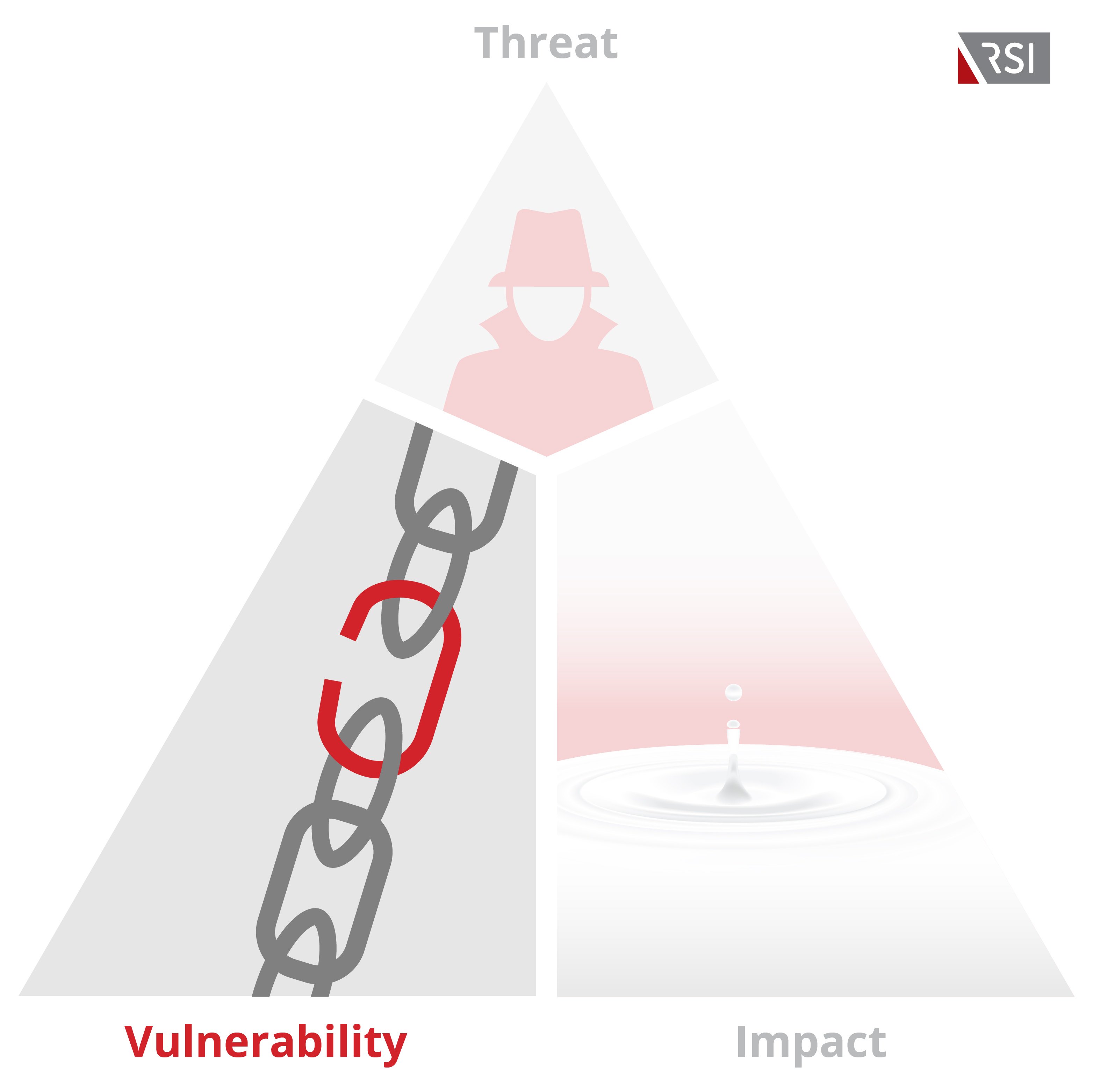
Identifying and understanding data security Vulnerabilities is fundamental to mitigate overall risk factors that confront your company on a daily basis. While you may have fortified your cyber defenses against viruses with AV or Malware software, and protected your perimeter from external breaches with an up to date hardware firewall, its also vital to understand the threats from within.
In previous blogs, weve outlined how your own workers can be a threat vector given accidental or deliberate attempts to access malicious websites. Security Awareness Training as well as Web content anti-phishing filters are valuable measures to both prepare your organization against these threats as well as counter them, when hackers inevitably make their way to your door.
Along with current and former employees, who else might have access to your systems? A particular threat vector that has emerged as a top concern is the third-party attack, also known as a supply chain attack. Think about all your partners and vendors that have access to your systems for the sake of various service maintenance and upgrades. What are your designated access controls? Do their credentials only grant them necessary access to specific areas of your network? Are you certain?
A number of prominent hacks were caused by a companys suppliers. Targets huge breach a few years back was due to stolen network credentials sourced from its HVAC vendor. The NotPetya malware breach earlier this year was attributed to a hacker compromising the integrity of a specific software package that a number of major corporations used. The tampered software was then pushed to companies as a legitimate update, which then allowed NotPetya to gain access and damage the victims network and system.
Not all third-party attacks has to be this sophisticated, or even electronic based. It can be as mundane as a law firms sub-contracted research firm mishandling paper documents with printed client Personally Identifiable Information (PII) on it.
The bottom line — if any other entity has privileged access / exposure to your clients sensitive information, then that data environment is also in scope and you are ultimately responsible for downstream breach ramifications and liability.
Addressing this issue starts first with a robust audit — understand what you have and what your partners / vendors may have. This happens less than we might hope. According to a recent study by Ponemon Institute, only 35% of companies were aware of the third-parties that they shared sensitive info with. As troubling, only 18% of companies knew if their vendors exposed their network or the original companys information to other vendors.
Because of these breaches, governments and regulators are stepping up with explicit privacy requirements and concrete punitive measures. The GDPR regulation, for example, imposes data privacy requirements on any company, anywhere in the world, to protect the personal data of EU citizens, even if the company doesnt conduct business in the EU. Does your database contain info on EU citizens, for any reason? If yes, youre automatically in scope, and liable for significant fines if your systems are breached and EU citizen data is revealed.
Call RSI to start a discussion of how we can help you understand the scope of your data environment. We can assess and optimize your access controls and work to limit your PII exposure by partitioning off a segment of your network. Whatever the required technical or policy mitigation, the first step is to have an assessment call with our security analysts that will prime deeper discussions into how to manage your third-party data vulnerabilities.
Get A Free Cyber Risk Report
Hackers don’t rest, neither should you. Identify your organization’s cybersecurity weaknesses before hackers do. Upon filling out this brief form you will be contacted by one of our representatives to generate a tailored report.
About the Author
 Eric Haruki is a technology analyst with over 15 years of experience advising global category leaderssuch as Samsung, Panasonic, HP, & Ciscoonproduct and brand strategy, market competitiveness, and in areas of untapped product and distribution opportunity. He has produced both syndicated and project work, delivering forecasts, SWOT analyses, road maps, and panel survey insights to research customers around the globe. Eric has contributed to major print and television press outlets and has been a featured presenter at industry conferences. He isdriven to find insights through extensive market research and deliver concise and actionable solutions to vendors, leading ultimately to the development of valued downstream goods and services to end users.
Eric Haruki is a technology analyst with over 15 years of experience advising global category leaderssuch as Samsung, Panasonic, HP, & Ciscoonproduct and brand strategy, market competitiveness, and in areas of untapped product and distribution opportunity. He has produced both syndicated and project work, delivering forecasts, SWOT analyses, road maps, and panel survey insights to research customers around the globe. Eric has contributed to major print and television press outlets and has been a featured presenter at industry conferences. He isdriven to find insights through extensive market research and deliver concise and actionable solutions to vendors, leading ultimately to the development of valued downstream goods and services to end users.

