The workplace is no longer an environment with stacks of filing boxes or employee mailboxes. Instead, files now speed through the Internet and meetings are held via teleconference. The ease of communication and multi-device compatibility, although convenient, increases the network vulnerability of companies. Understanding how a network operates, the components involved, and common threats will help companies prevent and mitigate future cyber attacks.
Is your online information secured? Read on to access our network security best practices checklist.
What Is Network Security?
Network security, at its heart, focuses on interactions — interactions between computers, tablets, and any other devices a company uses. Improving and maximizing network security helps prevent against unauthorized intrusions. SANS Institute defines network security as:
the process of taking physical and software preventive measures to protect the underlying networking infrastructure from unauthorized access, misuse, malfunction, modification, destruction, or improper disclosure, thereby creating a secure platform for computers, users and programs to perform their permitted critical functions within a secure environment.
More broadly, network security addresses who and what devices have access to the network. Securing network access ensures the integrity of data and transactions conducted on that network. A compromised network allows threat actors to obtain personal information that they can sell on the Dark Web. Personal information ranges from names and addresses to trade secrets and intellectual property, with each piece of information garnering a higher payout. Consequently, it’s vital to understand the threat landscape your company faces.
Assess your Network Security
Network Infrastructure
To combat network security threats and establish comprehensive policies, you must understand the components making up the network. Network infrastructure refers to the technology allowing devices to connect and interact; it primarily includes the hardware and software needed to enable communication between not only people, but also processes, applications, and external networks. Below are the key components of a network.
Hardware:
- Routers – Connects a network through a wide-area network (WAN) or a local area network (LAN). Routers use protocols to communicate and funnel data through the best route. Routers either use wireless or a wired connection.
- Switches – Creates a network and allows devices to communicate. For example, when you are at work and you send a document to print, it involves a message sent through a switch (i.e., transmits data).
- Hubs – A hub is technically a type of switch that forwards all network traffic to every device. It connects Ethernet devices via multiple ports. When one port receives a message packet, the hub copies that packet and allows all other ports to see the packet.
- Gateways – Link two or more networks by translating the signals/protocols of different networks
- Servers – Are central repositories for data and programs and can be used to manage the various devices on a network
Software:
- Firewalls – Program that controls network traffic based on a set of rules
- Intrusion Prevention systems – Programs that monitor the network traffic to find any suspicious activity
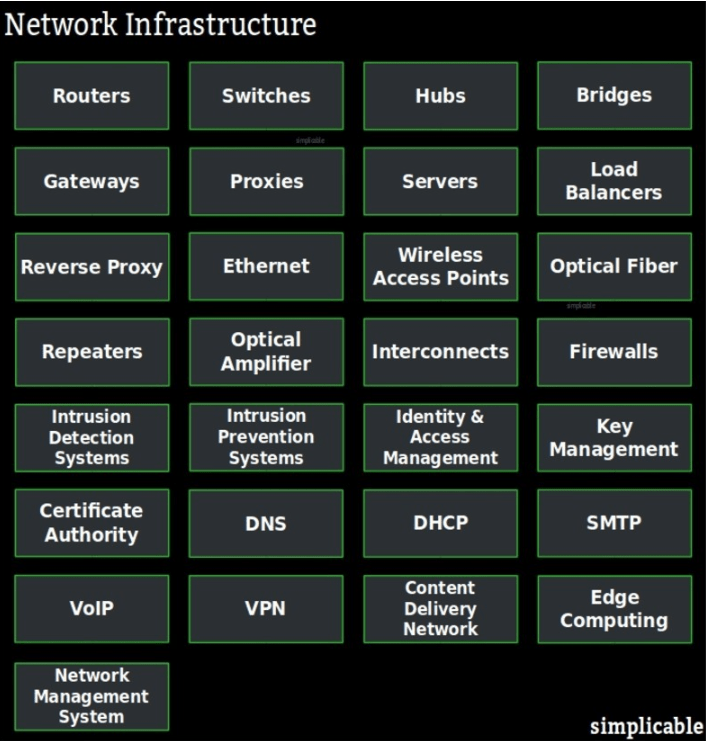
Graphic Source: https://simplicable.com/new/network-infrastructure
Basic Network Safeguards
Although some parts of a network are tangible, the intangible aspects sometimes make it difficult to grasp the extent of a threat until it’s too late. Malware, denial of service attacks, and remote control access are just a few of the various threats networks face. Below the basic best practices experts recommend for starting a network security policy.
- Anti-malware – It’s important to have constant vigilance for suspicious activity. Implementing anti-virus software and intrusion detection program will help guard against attacks. Additionally, having automatic backups and security updates will keep operating systems up-to-date on the most current patches.
- Passwords – Requiring strong passwords for all devices connected to a network is key. This includes passwords for control access, devices taken off-company premises, and remote access networks. NIST’s new password recommendations suggest using password phrases since they are often easier to remember but harder for threat actors to crack. Additionally, requiring a password change after at least 90 days is suggested.
- Monitoring and auditing – Auditing ensures that the safeguards in place are functioning properly and being maximized to protect the weakest links in the network. A yearly audit is recommended while monitoring (e.g., malware scanning) should be conducted throughout the year.
- Limiting remote access – Allowing others to have remote access to files may seem convenient, but if precautions are not taken, your network may become compromised. The Federal Trade Commission (FTC) recommends having a contractual set of security requirements for any persons or companies that need remote access. Setting access limits for only what an entity/person needs (e.g., contractor) and time limits (e.g., 1 month of access) is another way to tighten security.
- Mobile device/removable media policy – As the saying goes, “your network is only as secure as the least safe device that connects to it.” Without continuously reviewing policies and implementing training programs for employees, devices will fall behind the most up-to-date security protocols. Companies should train employees on best practices, automating security updates, and establish procedures for if/how devices are removed from the company buildings.
Common Network Security Mistakes to Avoid
Poor network security risks not only company assets but also reputation. Any expert will tell you there is no one size fits all option for network security. Rather security depends on vigilance, attention to detail, and, above all, a multi-layered strategy. Below are four common mistakes to avoid:
- Knowing network devices – It’s difficult to keep track of every device accessing a network, particularly for large companies. However, periodically taking inventory of devices will enable security teams to better identify suspicious activity and maintain an updated system. Understanding the access points will assist in identifying the weakest links.
- Stop delaying patches – While zero-day vulnerabilities remain a constant threat, they often overshadow the known threats that already have available patches. Known exploits are easier for threat actors to exploit and failing to implement an available security patch endangers company data. Experts recommend implementing a schedule for instituting patches or researching what new patches are available.
- Strategic structuring – cyber experts know it’s not a matter of if a breach will occur, but when. It falls to security teams to make sure when attacks happen that the network is structured defensively. For example, an attacker breaks through a firewall and, because the network is open once a person enters it, the attacker has unlimited access to the entire network. Implementing segmentation will wall-off an attackers’ mobility once they are in the system. Techopedia defines segmentation as the idea of creating sub-networks within a corporate or enterprise network or some other type of overall computer network. Think of segmentation as a “containment chamber” in a hospital. If a malware “disease” enters the system, you want to contain it and prevent it from spreading.
- Security team size – No matter how many safeguards you put in place, if you don’t have the people to monitor and manage them, they won’t be effective. For small companies, it is particularly difficult to maintain a robust security team. Using an external security company can help reduce costs or assist in the interim while a permanent security team is assembled.

How to Combat Human Error
A 2018 report by Proofpoint found that 95 percent of web-based attacks involve social engineering or take advantage of human error. Deceiving emails or enticing links often attract humans’ attention and can lead to serious network security breaches. According to NH Business Review, humans consistently make these five mistakes that compromise network security:
- Passwords are the bane of employees. How many times have you forgotten your password and needed to reset it? This leads employees to write their passwords down, use simple passwords, and even reuse passwords on multiple accounts. Passwords are important for work and non-work accounts. For example, if a person’s Facebook account is hacked because of an easy password, that person’s identity can be spoofed and used to invade or trick their work friends into granting the threat actor company network access. It is also unwise to use corporate passwords for personal/non-corporate accounts. Although the solution isn’t foolproof, try using a password generator and manager. This will ensure strong passwords are used and stored in a secure location. Additionally, keep an eye out for the annual Best Password Managers report(s) typically published by various tech magazines at the start of each new year.
- Unsecured WiFi entices workers and passersby alike because of its convenience. However, these networks do not typically undergo the same scrutiny that corporate networks do, allowing threat actors to more easily penetrate those networks. For example, if your company allows you to work remotely and you decide to go to a coffee shop, using any work applications on the shop’s WiFi is risky. It’s also risky to complete confidential transactions (e.g., banking) on public WiFi networks. What could you lose? Besides credentials, hackers could sift through files and potentially take files from the device. Sometimes using public WiFi networks is unavoidable (e.g., at an airport). In those situations, limit activity to only internet browsing or use a secure Virtual Private Network (VPN). Another option when on the move is to use a mobile hotspot, although this can affect mobile data billing.
- Phishing emails trick the public and employees every day. Most employees have likely experienced a phishing email at some point. Phishing emails attempt to lure users into clicking on a malicious link, downloading a corrupt file, or installing malware. The key is that phishing emails usually use personal touches to convince people that the email is legitimate. Employees are even more likely to open malicious emails if they appear to come from a superior. One of the best ways to combat phishing emails is to run simulations and train employees on analyzing emails. For example, if you think an email is internal, hover over the contact information before even opening the email to verify the address is legitimate.
- Professional social media, like LinkedIn, allow professionals to connect, but they also create another opportunity for threat actors to acquire personal information – this is a from social engineering. For example, a hacker may track an employee on LinkedIn, gain their trust, and then use personal information to send out a phishing email to the company. Informing employees about social media best practices will strengthen this hard-to-control network vulnerability.
- Inadvertently installing malware on a company device can occur in unexpected ways. For example, an employee may check a weather website before driving home and accidentally clicks on a pop-up ad. The ad, although seemingly harmless and quickly closed, may initiate malware installation on an employee’s device. Thus, the whole network is at risk. Patching known vulnerabilities and installing security scanners assist in mitigating these “drive-by” attacks.
A Layered Network Security Approach
As mentioned above, a dynamic strategy thwarts threat actors or at least makes it more difficult for them to compromise the entire network. The concept of a multi-layered approach to cybersecurity involves backups in case one security measure fails. Think of a ship’s water-sealing mechanisms. If there is a breach in the hull and one door fails, there is another air-tight door to take its place and either slow the inflow of water or completely stop it. Likewise, a multi-layered network security strategy implements targeted security measures (e.g., a firewall) that, on their own, have merit but when combined with all other security measures fill in any security gaps.
Layers should incorporate many of the security basics listed above including the following: patching , encryption , firewalls , email/web filters, and antivirus software. These measures are just the base level of security and must be implemented in concert. If only one or two are implemented, the security strategy is not classified as a layered approach. Companies should strive for layers that include mechanisms for not only detecting and reacting to security threats but also for proactively addressing security threats. Although it’s easy to jump right in and start changing security procedures, taking a few minutes to read about Proactive Network Maintenance will help strengthen your network security policy and ensure new procedures are implemented in a safe and efficient way.

Want to Learn More?
According to a 2018 report, the cybercrime economy is worth roughly $1.5 trillion per year, and experts expect a steady increase over the next few years. Additionally, it takes approximately 50 days for companies to identify a breach from when it occurred. With these sobering statistics, it’s important to re-evaluate your network security practices at least once a year. If you need help evaluating your current network security practices or need solutions to network security threats, contact RSI Security today.

