Besides texting and social media, email is the communication hub for workers around the world. It enables more efficient communication and scheduling as well as improving organization. Yet, in the chaos of daily operations, it’s easy to overlook the security of email systems. Is your email vulnerable to security threats? Find out our top email safety tips with our comprehensive guide from RSI Security.
The Rise of Email
The prototype version of email emerged in 1965 at MIT, but it wasn’t until 1973 that the government, like the US Defense Advanced Research Projects Agency (Darpa), began developing email standards. The term “email” didn’t appear until around 1979. The real game-changer came in 1988 when Microsoft released its first version of Microsoft Mail, which today is Microsoft Outlook and Microsoft Exchange. Since then, email has progressed, allowing people to forward messages, include attachments, schedule appointments, and so much more.
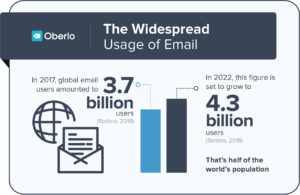
Image source: https://www.oberlo.com/blog/email-marketing-statistics
What Information Is at Risk?
Unfortunately, as with most technology, it was only a matter of time before a threat actor sought to exploit email. In the early 1990s, the first instance of email spam appeared. Today, attacks have become much more complex and damaging, considering how vital email is to operations and advertising. So what can a threat actor access through email?
Employee Concerns
At a minimum, an email breach can compromise an employee’s email address which is likely linked to numerous accounts both in and outside of a company. The email can then be used to access accounts or may be sold on the dark web. If an employee responds to phishing emails, many bits of information may be compromised. A lot of employees also have an electronic signature on their accounts listing their name, position, phone number, and sometimes the company address. All of this could be compromised by responding to a malicious email, not to mention the concern of initiating malware by clicking on a fraudulent link. Once a threat actor gains access to a system through email (and it only takes one employee to endanger a system), a threat actor may gain access to meeting times, read confidential/proprietary information, or impersonate an employee. The subsequent consequences aren’t pleasant to think about, but they are tangible threats that plague companies every day.
For Consumers
Consumers face many of the same email concerns as employees, but there are some notable distinctions. Consumers likely do not send proprietary information via a personal email account. However, they do send credit card statements, healthcare details, and other personal information (like pictures or videos) through emails. As a result, the threats are largely the same but involving different content and on a different scale. A threat actor may use a personal account to infiltrate the accounts of family members or friends. Another reason employee training is so important is that sometimes employees mistakenly send valuable information over personal emails.
Email Marketing Security
How many times have you been at a retail store and were asked, “Would you like to subscribe to our email list and get discounts?” Probably often. Email marketing gives companies a relatively cheap and effective means of advertising, increasing online shopping, and promoting sales. Even better, with the improvement of algorithms and AI, emails can now be personalized, making customers feel special.
Needless to say, companies love email marketing because it is a great RoI. A DMA report calculated that for every one dollar spent, a company receives approximately USD 32 in return! For Small to Medium Businesses (SMBs), email provides an affordable way to grow business. However, SMBs don’t always have the necessary safeguards for email security.

Email Safety Tips
To get started enhancing your email security policy, use the following email security checklist which includes the common best practices for companies and consumers alike.
Authentication – Make sure to use strong passwords or passphrases as well as 2FA. If a threat actor obtains an email address, the first thing they may do is try to guess the email password. Changing default passwords and avoiding common passwords will increase the difficulty of compromising an email account. To learn more about multi-factor authentication, check out RSI Security’s article on The Factors of Multifactor Authentication.
Avoid Public Networks – One of the great things about email is that communication bridges distances. When on the go, employees frequently log on to unsecured cafe networks to check their email or finish some work. However, not all these networks are properly secured. Some have passwords, but they aren’t always strong passwords. One safer option is to use a work phone’s mobile hotspot if sending sensitive information.
Physical Security – Desktops, laptops, or other devices at companies can be compromised when an intruder breaks into a facility. Passwords or other documents could be lying around or the intruder may install malware onto the devices. The bottom line is that every company should have security cameras, locks, log-on monitoring, and any other appropriate measures for protecting company premises. Additionally, train employees to clear their desks of any sensitive information (or lock it up) prior to leaving the office for the day.
Educate Employees and Customers about phishing – Phishing is a relatively cheap and easy method for hackers to gain personal information. According to Verizon’s 2018 Data Breach Investigations Report, 93 percent of social attacks were phishing and pretexting, with email being the most common attack vector.
Encryption – Using encrypted email should be common practice, especially for companies sending files, blueprints, etc. via email. You can use either built-in encryption or password encryption. You should encrypt the connection from your email provider, the messages, and stored/archived emails. Encryption isn’t just for companies, consumers can also benefit from encrypted email. Take the time to research the free and paid encryption options available.
Network Scanning – Network scanning enables IT departments to identify all devices on the network. Ping sweeps help identify the IP addresses of hosts connected to the network. Scanning helps identify any irregularities.
Patch Management – Cyber attackers like to use strategies that work, and known vulnerabilities are just that, reliable. Why? Because companies fail to implement patches as soon as they become available. A 2018 Verizon report found that most attacks exploit vulnerabilities six months or more after discovery. Patchings isn’t easy due to the plethora of vulnerabilities and patches being released on a daily basis, but by using threat prioritization, security teams can implement patches in a more effective and expedited manner.
Firewalls – Firewalls help protect systems from outside threats. This may be helpful if a malicious link, sent through an email, tries to download or initiate a program. Email firewalls regulate what mail is allowed through and flag certain content as spam based on a list of rules in the email server. An email firewall communicates with other servers alerting them if spam was sent or if it is incoming.
Documents at Offices – This may come as a surprise, but your email and other PII can be compromised at a doctor’s office. How? When you fill out documents on those communal clipboards, sometimes the imprint is left behind for others to see. Emails aren’t only at risk, insurance information and other health information can also be compromised in this manner. Anytime you are filling out documents at a public place on a common clipboard, make sure to remove papers underneath that may retain the imprint of your private information.
Email Authentication Trio
The commonly accepted forms of email verification are DKIM, SPF, and DMARC. These three work in conjunction to combat email spoofing, malicious links, and other malware. Although companies can implement these three security checks separately, it is highly recommended that all three are used together to maximize the benefits they offer.
Sender Policy Framework (SPF)
SPF strengthens DNS servers and reduces the likelihood of domain spoofing. It checks the identity of the sender to see if an incoming email originates from a legitimate domain. The framework blocks unsolicited, bulk emails. SPF includes a policy framework, an authentication method, and a header that specifies what information was found during the authentication process. The most recent SPF standard (IETF standard 7372) was released in 2014.
Domain Keys Identified Mail
Although Domain Keys Identified Mail (DKIM) identifies whether an email was sent and authorized by an authentic domain owner, it also checks the integrity of the message. DKIM assigns a digital signature at the top of an email with encryption. The signature is not typically visible to email users; rather, it is validated on a server level. In this way, DKIM verifies the integrity of the content and attachments of an email.
Domain-based Message Authentication, Reporting & Conformance
Domain-based Message Authentication, Reporting & Conformance (DMARC) verifies that emails follow SPF and DKIM standards. DMARC involves domain alignment and reporting. The alignment process stops emails with spoofed “from” headers by comparing the domain name sender information with the SPF check information. DMARC relies on the implementation of SPF and DKIM.
Email Regulatory Compliance
Although legislation solely addressing email security does not exist, many of the privacy laws in place, either have specific clauses for email security or email automatically falls under the privacy specifications. Among these are the Sarbanes-Oxley (SOX) or The Patriot Act, the European Union Data Protection Directive, HIPAA, GLBA, and PCI DSS. In addition to these regulations, several well-known research institutes and industry leaders have published best practices regarding email security. A few examples include the Committee of Sponsoring Organizations of the Treadway Commission (COSO), the Information Systems Audit and Control Association (ISACA), the National Institute of Standards and Technology (NIST), and the International Organization for Standardization (ISO).
Cloud Email Security
Many companies utilize cloud-based email services because they require no server maintenance, enable easier disaster recovery, offer access from any device, and improve collaboration. Moreover, cloud security is a cost-effective means for reducing spam, depending on which cloud provider a company chooses to use. In order to reduce spam, cloud providers typically utilize RBL and SUBRL filters, which compare incoming mail IP addresses to blacklists. Cloud email security provides IT departments with customization options. For example, spam thresholds can be adjusted and adaptive spam filtering applied.

Two-Way Email Security
Email security does not only focus on incoming emails. Two-way email security analyzes both incoming and outgoing emails with the goal of identifying any compromised accounts. A malicious email may trigger a massive spam campaign within the company or send malicious emails to customers. One of the biggest things a threat actor can leverage, if it infiltrates a company’s system, is trust. Company emails typically garner more trust and people accept them more easily without suspicion. Losing that trust and credibility may impact a company more than the monetary cost of the breach.
NIST Password Recommendations
Although the warning of using strong passwords seems like a song constantly on repeat, it’s worth taking a minute to note. Password recommendations change as threats change. Just a few years ago, the common practice was to include mostly random numbers and symbols and to change passwords every few months. But now, experts are beginning to promote passphrases. NIST’s Special Publication 800-63 covers everything from multi-factor authentication to threats to privacy. Below are a few key recommendations when it comes to crafting a password policy and training employees.
- 8 character minimum for human-set passwords and 6 character minimum for machine-generated passwords
- Do not truncate passwords when processing
- Set a 10 attempts limit for entering password
- Do not use password hints
- Do not use SMS for 2FA (SMS has significant vulnerabilities)
- No complexity requirements
Passphrases vs Passwords
Passphrases have become more popular recently because they are easier to remember yet still difficult to crack. For example, a typical password includes many symbols, numbers, and upper/lower case letters. In contrast, a passphrase contains fewer components and is longer but easier to remember like, “Thebookwormlivesatthelibrary.” People can select phrases that mean something to them or are just catchy, making it easier to remember and not necessary to write it down. Passphrases address the issue that a Stack Exchange user aptly quipped, “Security at the expense of usability comes at the expense of security.”
Need Help?
Email security should be a part of any well-rounded cybersecurity policy. If you are interested in learning more about email safety tips or would like to conduct a risk assessment, contact RSI Security today for a consultation.

