The new Cybersecurity Maturity Model Certification (CMMC) is meant to simplify the process of compliance for all companies who work with Federal Contract Information (FCI) and Controlled Unclassified Information (CUI) along the Department of Defense (DoD) supply chain. An explanation of what is considered CUI is in the Organization Index Grouping of Defense that can be found here. Draft v0.7 has been released, and the final draft, v1.0, is slated for release in January 2020. It is recommended that companies review v0.7 to begin to prepare for compliance dependent on the level of DoD CMMC certification that will be required for them to be able to bid projects.
Draft v0.7 is available on the Internet in its entirety. What follows, however, is a brief synopsis of the information contained in that release along with insights from Katie Arrington, Special Assistant to the Assistant Secretary of Defense for Acquisition for Cyber, Office of the Under Secretary of Acquisition and Sustainment, in her webinar recorded July 17, 2019, called “What Contractors Need to Know About DoD’s CMMC.” (You must be signed in as a user to view the webinar.)
In her webinar with the Professional Services Council on July 17, 2019, called “What Contractors Need to Know About DoD’s CMMC,” Katie Arrington stated that the loss of CUI that results from poor cybersecurity controls amounts to over 600 billion dollars every year. Though the DoD CMMC certification process will be costly, it is estimated that it will save more than it will cost. The government is also willing to absorb the cost of DoD CMMC certification in its bidding process and will consider that cost as an allowable expense. The Request For Information and Request For Proposal sections L and M will specify the level of DoD CMMC certification required for a particular project and will be a go/no-go decision-making status for bids.
Assess your CMMC compliance
Level Up
The new CMMC process will require compliance at varying levels depending on the sensitivity of information and goods disseminated by companies along the DoD supply chain. It is estimated that over 300,000 companies, small and large businesses alike, will require this new certification. That is anyone dealing with the DoD or who is subcontracted by a company that has been directly contracted by the DoD will be required to comply. Certification is supposed to be made easier by this process, funneling in the various pre existing standards for compliance such as the NIST 171, 53, FedRAMP, ISO 9000 and others.
“The CMMC effort builds upon existing regulation, specifically, 48 Code of Federal Regulations (CFR) 52.204-21 and Defense Federal Acquisition Regulation Supplement (DFARS) 252.204-7012, and incorporates practices from multiple sources such as the National Institute of Standards and Technology (NIST) Special Publication (SP) 800-171 rev 1, Draft NIST SP 800-171B, the United Kingdom’s Cyber Essentials, and Australia’s Essential Eight.” (Cybersecurity Maturity Model Certification (CMMC) DRAFT Version 0.7 December 6, 2019, page 1)
Importantly, DoD CMMC certification will be offered by third-party companies and managed by an independent non-profit designated by the DoD. As of today, that designation has not been made, but when the DoD moves forward with that decision it is expected that third-party companies who already certify compliance to existing standards will step up and take on this new certification process. The independent nonprofit will be in charge of training the auditors and certifiers to comply with DoD CMMC requirements. Companies like RSI Security that are responsible for remediation to standards in these requirements will then be able to assist other companies in implementing the required controls for their desired level of CMMC compliance, with Level 5 being the most difficult level to achieve with the greatest number of controls, and Level 1 being the least difficult level to achieve with the least number of controls.
Download our CMMC Whitepaper: Best Cybersecurity Practices for DoD Contractors
The purpose of the levels is to only make a company comply with DoD CMMC requirements that are necessary to protect the type of CUI they handle. For example, a vendor at the bottom of the supply chain who sews eyelets onto military boots may only be required to certify to a Level 1, whereas someone who produces the whole boot and ships the boots to their destination, the CUI in this case, would be required to certify to a higher level. (For an idea of what some current best practices are in protecting CUI, consult NIST’s “FAQ for Protecting Controlled Unclassified Information (CUI).”)
Both practices and processes will require DoD CMMC certification. If practices and processes are not certified at the same level, the certification will be at the lower level. Also, each level builds upon the next such that all the DoD CMMC requirements of every lower level must be fulfilled in addition to new requirements at the higher level of certification desired.
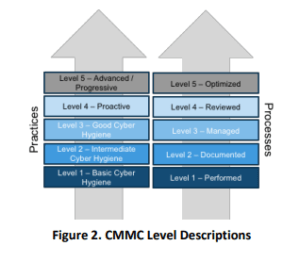
Image is from Cybersecurity Maturity Model Certification (CMMC) DRAFT Version 0.7 December 6, 2019, page 2.
Level 1 – Basic Cyber Hygiene/Level 1 – Performed
CMMC Level 1 is based on 48 CFR 52.204-21. The basic requirements of Level 1 are foundational to all the levels and must be completed by every company along the DoD contractor supply chain in the Defense Industrial Base (DIB).
There is no process maturity requirement at this level.
Level 2 – Intermediate Cyber Hygiene/Level 2 – Documented
CMMC Level 2 is a more advanced and mature version of Level 1 with the introduction of documentation to processes including SOPs, policies, and strategic plans.
Level 3 – Good Cyber Hygiene/Level 3 – Managed
CMMC Level 3 indicates adherence to ALL security control requirements in NIST SP 800-171 Rev 1. Any company that handles CUI is required to achieve Level 3 certification. Also, if a company is subject to DFARS clause 252.204-7012, it will still have to comply with those requirements, e.g., incident reporting.
Level 3 also consists of adherence to a CMMC process maturity model where audits to policy and procedures exist.
Level 4 – Proactive/Level 4 – Reviewed
CMMC Level 4 companies can demonstrate a proactive cybersecurity approach that includes adapting their protection and sustainment activities to Advanced Persistent Threat (APT) Tactics, Techniques, and Procedures.
Level 4 CMMC maturity indicates review and review documentation informs upper management of issues requiring remediation.
Level 5 – Advanced/Progressive/Level 5 – Optimized
CMMC Level 5 indicates a responsive and adaptable company that uses optimized cybersecurity controls to fight against APTs.
Process level maturity at this most advanced level indicates the company that has been DoD CMMC certified ensures processes have been standardized and implemented uniformly across their entire company.
Organization and Compliance to DoD CMMC Requirements – Domains
There are 17 domains in which practices and processes for the various levels must be implemented: Access Control (AC); Asset Management (AM); Audit and Accountability (AA); Awareness and Training (AT); Configuration Management (CM); Identification and Authentication (IDA); Incident Response (IR); Maintenance (MA); Media Protection (MP); Personnel Security (PS); Physical Protection (PP); Recovery (RE); Risk Management (RM); Security Assessment (SAS); Situational Awareness (SA); System and Communications Protection (SCP); and System and Information Integrity (SII).
Each domain has several cybersecurity capabilities that CMMC practices may exist within. Some of the domains do not require practices for every capability at every level of certification.

Image is from Cybersecurity Maturity Model Certification (CMMC) DRAFT Version 0.7 December 6, 2019, page 6.
The specific practices required for each of the domains can be found in Appendix A of the “Cybersecurity Maturity Model Certification (CMMC) DRAFT Version 0.7 December 6, 2019.” This blog will simply detail a few examples to help companies get a better idea of the types of practices required at the various levels of a couple of domains.
Reading the charts in Appendix A is simple to do. Look up the control domain of interest, scroll down to find the capability that requires compliance, then scroll across to the level of DoD CMMC certification sought. Remember that all lower-level practices will be required at a higher level. So, record all practices at every level for that capability. Note that some capabilities will not require practices at all levels, so it’s okay if a cell is blank.
Example 1: Domain AC
For example, the first focus of a company’s DoD CMMC certification preparation could be the Domain AC and the capability of interest could be C002 Control Internal System Access. This company’s desired level of DoD CMMC certification is a Level 5 because they deal with nonpublic sensitive FIC and CUI. Scrolling across to Level 1, P1002 explains the practice for this capability at Level 1. This practice must be included for the Level 5 certification, as well as all practices for Levels 2, 3, and 4. The practice is to “Limit information system access to the types of transactions and functions that authorized users are permitted to execute,” and below the practice identified by bullet points are the pre existing practices from other regulatory agencies that helped to inform the practice explained. They are FAR Clause 52.204-21 b.1.ii and NIST SP 800 171 3.1.2. This is just for reference.
Scrolling across to Level 2 for this capability, there are five more practices, each in their own cells, each followed by a bulleted list of standards that informed the CMMC practice. They are P1007, P1008, P1009, P1010, and P1011. P1007 indicates that a company should “Employ the principle of least privilege, including for specific security functions and privileged accounts.” This best practice is informed by NIST SP 800-171 3.1.5 and UK NCSC Cyber Essentials. P1008 indicates that a company should “Use non-privileged accounts or roles when Assessing nonsecurity functions.” This practice is informed by NIST SP 800-171.3.1.6 and UK NCSC Cyber Essentials. P1009 indicates that a company should “Limit unsuccessful login attempts.” This practice is informed by NIST SP 800 171 3.1.8. P1010 indicates that a company should “Use session lock with pattern-hiding displays to prevent access and viewing of data after a period of inactivity.” This particular practice is informed by NIST SP 800-171 3.1.10. P1011 indicates that a company should “Authorize wireless access prior to allowing such connections.” This is informed by NIST SP 800-171 3.1.16.

Scrolling across to Level 3, there are five more CMMC practices listed for C002: P1017, P1018, P1019, P1012, and P1020. P1017 indicates that a company should “Separate the duties of individuals to reduce the risk of malevolent activity without collusion.” This practice is informed by NIST SP 800-171 3.1.4. P1018 indicates that a company should “Prevent non-privileged users from executing privileged functions and capture the execution of such functions in audit logs.” This practice is informed by NIST SP 800-171 3.1.7. P1019 indicates that a company should “Terminate (automatically) user sessions after a defined condition.” This practice is informed by NIST SP 800-171 3.1.11. P1012 indicates that a company should “Protect wireless access using authentication and encryption.” This practice is informed by NIST SP 800-171 3.1.17. P1020 indicates that a company should “Control the connection of mobile devices.” This practice is informed by NIST SP 800-171 3.1.18 and UK NCSC Cyber Essentials.
Now Level 4 only has two more CMMC practices, P1023, and P1025. P1023 indicates that a company should “Control information flows between security domains on connected systems.” This practice is informed by NIST SP 800-171B Partial 3.1.3e. P1025 indicates that a company should “Periodically review and update CUI program access permissions.” The CMMC after the bullet indicates that this practice is informed by the work of the CMMC committee during the production of the CMMC.
Finally, scrolling across to Level 5, there is one more CMMC practice indicated. P1024 indicates that a company should “Identify and mitigate risk associated with unidentified wireless access points connected to the network.” This practice is informed by CIS Controls v7.1 15.3.
Example 2: Domain AM
Another good example is the Domain AM and Capability C006 Manage Asset Inventory. No practices are indicated for Levels 1, 2, and 3. This means to be DoD CMMC certified at any of those levels does not require compliance with any DoD CMMC requirements practice for that capability. For Level 4 P1226 is indicated. This practice indicates that the company seeking DoD CMMC certification should “Employ automated capability to discover and identify systems with specific component attributes (e.g., firmware level, OS type) within your inventory.” This practice is informed by CMMC modification of NIST SP 800-1718 3.4.3e. However, again for Level 5, no practice is indicated. So, to be DoD CMMC certified at Level 5 in this capability, a company would only have to adhere to P1226 from Level 4.
Help With DoD CMMC Requirements
The goal of the CMMC is not to add extra burdens to the private sector contractors in the DIB through complicated DoD CMMC requirements. The goal is to simplify and streamline the process so that it becomes more efficient for everyone involved. Hopefully, the information we presented will put you more at ease in the face of the new compliance regulations. And they are coming in January of 2020 with implementation set to begin in some RFIs as early as June 2020. Hence, the time to get going on certification preparations is now.
The CMMC only explains WHAT practices a company must implement. It does not explain HOW to implement them. That’s why the services of a cybersecurity solutions implementation expert like RSI Security are crucial. RSI Security understands the CMMC inside and out and will prepare you to take your company to the level of DoD CMMC certification you seek. Contact RSI Security today to find out how to make your business more profitable by making it more secure.
