Healthcare is an industry intertwined with our everyday lives. The young and the old alike rely on doctors to keep them healthy and usually, in that pursuit, reveal personal details to their health practitioners. This means consumers put a lot of trust in healthcare companies.
But with technology taking over the mundane tasks of healthcare, threat actors target health institutions for that personal information. The Health Information Trust Alliance (HITRUST) is designed to verify privacy and security compliance combat healthcare fraud. In particular, there are three different levels associated with HITRUST controls.
Learn about each HITRUST level and why it’s important with our comprehensive guide.
What Does HITRUST Provide?
The Health Insurance Portability and Accountability Act (HIPAA) may outline healthcare privacy guidelines, but it leaves monitoring and verifying compliance with independent entities. Likewise, many other security regulations lack a verification process. Given the number of healthcare data breaches, it’s clear vendors and covered entities struggle to implement proper security protocols. That is where HITRUST comes in.
HITRUST is composed of healthcare industry leaders striving for a more coherent approach to healthcare security. In pursuit of this goal, the Alliance developed a security evaluation process that, once completed, gives healthcare providers a certification. This certification verifies that the company followed the Common Security Framework (CSF). The CSF serves as a standardized security framework collating many regulations into one process. The latest version, 9.3, consolidates multiple regulations including the California Consumer Privacy Act and NIST Cybersecurity Framework.
Assess your HITRUST compliance
Is HITRUST Worth it?
With numerous audits and frameworks available, it’s reasonable to wonder what sets HITRUST certification apart from the others. In short, HITRUST is a one-stop-shop for healthcare security compliance, or at least very comprehensive. The current HITRUST certification covers NIST, HIPAA, HITECH, ISO 27001, PCI DSS, FTC, COBIT, and SOC 2.
Having access to personal health information and financial information makes healthcare entities prime targets and just one vulnerability can cause significant damage. Consider how a ransomware attack could impact just one hospital. With patient care dependant on access to Electronic Personal Health Information (ePHI), hospitals would likely pay the demanded ransom to save lives.
Beyond information, the Medical Internet of Things (IoT) is also at risk. Devices can now connect from a patient’s home and transmit biometric data to health professionals. What if these devices are compromised? The ramifications are grim, and that’s why HITRUST is so important. It covers healthcare compliance from many different angles.

The Three HITRUST Levels
Part of the CSF includes three implementation levels. The levels differ depending on the level of risk. The higher the risk, the greater the control restrictiveness. HITRUST divides risk into three categories: organizational, system, or regulatory risks. When all three types of risks are considered, they determine which implementation level is appropriate for a certain control.
Companies seeking HITRUST compliance must, at a minimum, comply with level one. It should be noted that because of the breadth of HITRUST’s certification, some regulations do not apply to certain entities. For example, if a company does not use contractors, the contracting regulation section of the CSF is irrelevant. Below are the risks that help determine if level one, two, or three are necessary for a certain control.
Organizational risk factors
Organizational risk factors address the size of an entity both in geographic scope and volume. In terms of geographic scope, look at where your company operates. Does your company only operate within one-state, many states, or internationally? In terms of the volumes of business, analyze the number of facilities, patient visits, transactions per year, or the number of lives covered. Whatever sector of the health industry, volume refers to the extent of operations both on the business and consumer side.
Regulatory risk factors
Regulatory risk factors are determined by organizational and system specifications. For example, a large company, operating internationally, and utilizing intricate systems would earn a higher risk level (three) and face a more rigorous process for certification. But as is in the name, the level of implementation is specific to each control, and each set of regulations within the CSF mandates different controls. PCI, FISMA, HITECH breach notification, and individual state regulations are just a few of the many regulations HITRUST includes.
System risk factors
System risk factors change based on system attributes. As most companies utilize multiple systems, each system, unless functioning in a group of systems, will be assigned a level. Attributes cover everything from internal to external systems. Storing, processing, and transmitting PHI falls are classified as system risks, as well as mobile device usage, public websites, and third-party access. Other considerations are how many users visit your companies website or the number of transactions that take place on your platform.
How the Levels Work
Level one is the base level upon which recommendations or level upgrades are built. The most comprehensive level is three. Each level includes the previous level or levels plus any additional recommendation. The CSF’s implementation levels is designed to reduce the ambiguity and subjectivity of “acceptable” threat mitigation. Implementation levels are assigned to each of the 135 controls listed in the CSF. Those controls fall under 19 different categories, including mobile devices, logging/monitoring, incident management, configuration, endpoint protection, and wireless protection.

How Often is HITRUST Certification Required?
Unlike HIPAA, HITRUST provides a certification, which makes it more meaningful in the eyes of investors or the public. General HIPAA forms only require companies to voluntarily confirm that they are compliant, meaning there isn’t an official verification process. But leaving compliance assessments to companies themselves can leave gaps for negligence. To offer more validity, companies turn to HITRUST, which as mentioned above covers HIPAA and much more. The certification lasts for two years.
Are There Penalties?
Since HITRUST is an amalgamation of regulations, it approaches penalties differently than typical government regulations. Because HITRUST is not a government certification, there is no one single authority that determines the severity of the penalty. It falls on the healthcare industry itself to determine the penalty equal to the level of a security breach unless the breach is of a government law like HIPAA. The complication stems from the extensive nature of HITRUST, as it covers far more regulatory domains than HIPAA.
HITRUST Certification Process
The HITRUST certification process changes from entity to entity. HITRUST allows companies to uniquely tailor the CSF to fit their size, systems, and customer base. The following five steps outline how a general HITRUST certification process proceeds.
- Evaluate: Evaluate the scope of your business and determine what expectations must be met.
- Adjust: After evaluating your company’s capabilities and systems, make adjustments using the MyCSF tool. The MyCSF tool is a software as a service (SaaS) product that allows companies to input their specifications and receive an output of which controls and requirements they must fulfill.
- Self-Audit: Once a list of controls is provided, conduct a self-audit using the HITRUST self-assessment tool to determine where there are gaps or if controls are missing entirely. Another option at this stage is to hire a CSF assessor to conduct the audit.
- Remediation: Simply completing a self-audit is not enough. Entities must take the key findings of an audit and research the best ways to strengthen the weak areas. In order to determine if the systems and operations are acceptable, entities must compare the internal audit findings to the MyCSF requirement list. Based off of the comparison, entities should make adjustments.
- Validation: Request a CSF assessment and validation. To begin the final validation process, entities must purchase a HITRUST CSF Validated Assessment and hire a CSF assessor. After the Validated Assessment is completed via the MyCSF tool, the assessor will review the controls in place and submit his/her findings to HITRUST. Lastly, HITRUST will provide a CSF Assessment report and, based on the score, issue a HITRUST certification letter or not.
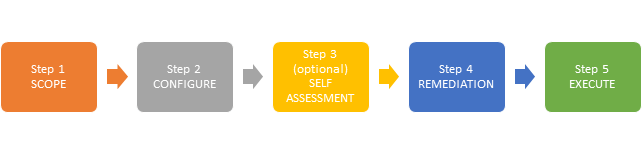
Image Source: http://www.isoqarindia.com/hitrust
HITRUST Self Assessment Tool
As noted above, companies have two options to begin the HITRUST certification process: 1) a self-audit, or 2) hire a CSF assessor.
In the case of self-auditing, HITRUST provides a comprehensive self-assessment process through the MyCSF tool. The self-assessment comes in various levels but is designed to catch any weak areas prior to the final Validated Assessment that determines certification. CSF self-assessments cost between USD 2,500 – USD 8,500. Options range from a report-only self-assessments to yearly subscriptions. The cost for a yearly subscription starts at USD 10,000 for small companies but can go up to USD 32,000 per year. The benefit of a subscription is that information logged in the MyCFS tool remains intact versus being deleted after 30 days, as is the case with the report-only option.
A self-assessment timeline changes depending on a company’s size, and the number of suggested controls will similarly vary. However, the typical number of controls for companies performing the lowest level of self-assessment is approximately 120-140 controls. Basically, this means a self-assessment will take a significant amount of time and commitment. For each control, the process, evidence, and maturity levels must be reported. This information isn’t usually all in one department, making communication crucial during the assessment process. A low estimate of a self-assessment duration is 120-140 hours if each control is given 60 minutes.
What HITRUST Offers
HITRUST is not just a certification organization. It offers many other resources for companies to use. You may not need a HITRUST assessment but are interested in security training. Talking to a security professional will help you choose which HITRUST option is best for your company’s needs. Below are the different services HITRUST provides.
- HITRUST CSF Self-Assessment – As noted above, HITRUST offers various levels of self-assessment to pinpoint the weaknesses in systems and operations.
- HITRUST CSF Validated Assessment – The Validation Assessment is the one that provides the actual certification. During the assessment, companies undergo onsite interviews, documentation reviews, and system testing.
- Readiness Assessment – This does not include a HITRUST report and is also called a pre-audit.
- MyCSF – MyCSF is vital to many of HITRUST’s services. It determines a company’s scope, helps document tests, and assists in monitoring remediation.
- CSF Practitioner Training – For companies not yet sold on HITRUST’s certification, companies can learn more about the CSF methodologies and the scoring process used.
- Remediation Tracking – After identifying weakness, it’s important to monitor the adjusted controls. HITRUST’s process and systems enable companies to track, report, and document any corrective actions.
- HITRUST Third-Party Assurance Program – This program allows companies to assess and monitor third-party or business partner activity.
- HITRUST CSF Assessor Firm – If you have the monetary resources but not the time to thoroughly complete the CSF certification, a HITRUST CSF Assessor firm can be hired to complete everything from the initial assessment all the way to remediation.
Healthcare Threats
HITRUST certification isn’t foolproof, but it helps minimize the gaps that piece-meal regulations sometimes cause. Below are five common threats to the healthcare industry that CSF certification will help combat.
- Cloud security – The cloud stores information for maximum accessibility, but it also makes it easier for attackers to intercept or compromise that data. In the past, attackers would have to analyze a physical location for weaknesses. Now, with a much more spread out data pool, attackers have more doors through which to go through.
- Mobile devices – One compromised mobile device can allow a threat actor to infiltrate a healthcare provider’s network and compromise customer ePHI. Security experts recommend augmenting existing phone security features by adding another layer of authentication.
- Ransomware – Besides potentially locking out healthcare records or other lifesaving systems, the ransomware threat becomes more concerning with regard to the black market. Personal information like healthcare information is particularly valuable on the black market thus making any entity with that information a prime target. Analyzing traffic patterns will help security experts identify if a ransomware attack occurs.
- IoT Exploits – The Internet of Things (IoT) offers so much possibility for patients in need of constant monitoring. Unfortunately, maintaining endpoint security for IoT devices is difficult and, if compromised, can endanger a patient’s life, both physically or in terms of stealing personal data.
- People – Employee cybersecurity training is essential. Running drills without telling employees and then assessing how security policies were followed will help improve employee awareness and better protect customer information.
Need Help?
HITRUST certification is a valuable asset for healthcare companies. Regardless of different clientele, hospitals, health insurers, biotech companies, and pharmaceutical companies all have one thing in common — they have personal health information that hackers want. HITRUST helps reassure consumers, investors, and business partners that your company cares about its responsibility to protect PHI. If you want to start the HITRUST certification process or have questions about the benefits of certification, contact RSI Security today.
Download Our HITRUST Compliance Checklist
Assess where your organization currently stands with being HITRUST compliant by completing this checklist. Upon filling out this brief form you will receive the checklist via email.

